FIX protocol implementation is no longer just a connectivity decision. It is a strategic architecture choice that shapes execution quality, scalability, and competitive positioning across capital markets.
Here is what the data shows right now:
Most FIX implementations fail not because the protocol is flawed, but because teams treat it as a simple API. They miss the session layer, undersized infrastructure, and skip certification steps. The result is latency, gaps, and failed connectivity when markets move fast.
This guide covers everything a CTO or Head of Technology needs — from trading platform architecture design to integration models, infrastructure requirements, security, cost planning, and future-proofing. If you are building, modernizing, or re-platforming a trading system, this is where you start.
What Is FIX Protocol and Where It Fit in Modern Trading Platform
The Financial Information eXchange (FIX) protocol is an open messaging standard created in 1992 to standardize the electronic exchange of financial information between institutions. Today, it governs the flow of orders, executions, allocations, and trade confirmations across brokers, exchanges, and asset managers globally.
Unlike proprietary APIs that vary by vendor, FIX is universally understood. It creates a common language for institutional trading — enabling a single integration that connects to hundreds of counterparties. That is the core purpose of the FIX protocol: to reduce integration friction without sacrificing execution control.
FIX in the Trading Stack
Understanding FIX means understanding where it lives in the full trading stack:
- Order Management System (OMS): Receives and tracks internal order flow. FIX carries orders from the OMS to downstream systems.
- Execution Management System (EMS): Routes orders to exchanges and brokers. FIX is the primary protocol for execution messages.
- Market Data Layer: Some implementations use FIX for real-time market data subscriptions (FAST/FIX).
- FIX Engine: The middleware that handles session management, message sequencing, and connectivity.
- Post-Trade Systems: FIX messages flow downstream for clearing, settlement, and reporting.
Purpose of FIX Protocol in 2026 Architectures
In 2026, the purpose of FIX protocol has expanded beyond order routing. Firms now use FIX for pre-trade risk checks, smart order routing signals, and real-time compliance validation. It has become a data-rich layer that feeds AI-driven execution intelligence. The shift is from messaging to infrastructure.
Core Components of a FIX-Enabled Trading Platform Architecture
A well-designed trading platform architecture built on FIX has five integrated layers. Each one must be engineered — not just deployed — to support institutional-grade performance.

OMS, EMS, and Order Routing Layer
The OMS manages the full order lifecycle — allocation, compliance, and status tracking. The EMS sits below it, focused on execution quality and speed. The order routing layer uses FIX session connectivity to distribute orders across venues based on pre-defined logic or smart routing algorithms.
Common failure point: OMS and EMS systems are tightly coupled to FIX logic. When the protocol updates or a new venue is added, this creates a change risk across multiple systems. Decouple them via an abstraction layer.
FIX Engine and Session Layer
The FIX protocol engine is the core middleware that manages sessions between counterparties. It handles Logon/Logout sequences, Heartbeat monitoring, sequence number tracking, and gap recovery. A well-implemented FIX engine is invisible — it runs consistently, handles edge cases, and never drops a message.
Key design choice: Threading model. A single-threaded engine is simpler but creates bottlenecks under load. Multi-threaded designs improve throughput but require careful synchronization to avoid sequence number corruption.
Market Data and Execution Gateways
Market data gateways feed real-time price information into the order routing logic. Execution gateways handle trade confirmation, fill reports, and rejection handling. Both must be latency-optimized and fault-tolerant. A missed fill report is not just a data gap — it is a compliance risk.
Post-Trade, Clearing, and Reporting Systems
FIX does not stop at execution. Post-trade workflows — including allocation, confirmation, and clearing — all rely on FIX message flows. For T+1 settlement environments, speed and accuracy here are non-negotiable. Gaps in post-trade FIX implementation create reconciliation failures and regulatory exposure.
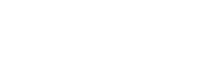
FIX Protocol Implementation Flow: Step-by-Step Guide
This FIX protocol implementation guide walks through the end-to-end lifecycle. Most failed implementations skip or rush at least one of these stages.
Step 1: Session Layer Setup — Logon, Heartbeat, Logout
The session layer is the foundation. Configure your Logon message (MsgType=A) with the agreed-upon CompIDs, HeartBtInt (heartbeat interval), and ResetOnLogon settings. Set the heartbeat interval based on your SLA — typically 30 seconds for standard connections, lower for latency-sensitive setups.
Heartbeat monitoring detects broken connections. If a heartbeat is missed, the engine sends a TestRequest. If no response arrives, the session terminates. This logic must be hardened against network flaps and clock drift.
Step 2: Message Flow and Data Mapping — Tags and Fields
Every FIX message is a structured set of tag-value pairs. For order flow, the critical tags are:
- Tag 11 — ClOrdID (Client Order ID, must be unique per session)
- Tag 38 — OrderQty
- Tag 40 — OrdType (Market, Limit, etc.)
- Tag 44 — Price
- Tag 54 — Side (Buy/Sell)
- Tag 55 — Symbol
Map your internal data model to these tags precisely. Mismatches here — wrong data types, missing required fields, or incorrect enumerated values — cause immediate session-level rejections. Build validation into the mapping layer, not as an afterthought.
Step 3: Validation, Sequencing, and Gap Recovery
FIX uses persistent sequence numbers to guarantee delivery order. Every message gets a MsgSeqNum. If the receiver detects a gap — for example, it receives sequence 105 after 102 — it issues a ResendRequest (MsgType=2). The sender must then replay the missing messages from persistent storage.
This requires a reliable message store. Do not use in-memory stores for production. Use disk-persisted or database-backed stores that survive crashes. Gap recovery latency directly impacts execution quality during volatile markets.
Step 4: Error Handling and Resilience Mechanisms
FIX implementations must handle three categories of errors: session-level (e.g., bad sequence numbers), application-level (e.g., unknown order IDs), and transport-level (e.g., TCP disconnects). Each requires a distinct response.
Design your error handling state machine before writing code. Common mistakes: treating all errors as fatal, failing to differentiate reject types (Reject vs. BusinessMessageReject vs. OrderCancelReject), and not logging enough context for post-incident analysis.
#FRAMEWORK: End-to-End FIX Implementation Lifecycle — Discovery → Session Config → Message Mapping → Validation → Certification → Production → Monitoring
Integration Models for FIX Connectivity
FIX API integration is not one-size-fits-all. The connectivity model you choose affects latency, cost, operational overhead, and scalability. There are three primary patterns.
Direct Exchange Connectivity
The lowest-latency option. Your FIX engine connects directly to the exchange matching engine via a co-located or proximity-hosted connection. Ideal for high-frequency strategies and market-making. Requires dedicated certification for each venue.
Hub-and-Spoke Model
A buy-side firm consolidates all broker and exchange connections through a single FIX hub. This is the most common model for asset managers. One certified integration manages N downstream venues. Reduces certification burden and operational complexity.
FIX Gateway / API Layer Approach
A translation layer sits between internal systems and external venues. The gateway normalizes message formats, handles version differences between FIX 4.x and 5.0, and provides centralized monitoring. Best for firms with diverse internal systems or multi-asset trading.
Actionable Insights Table
| Model | Latency | Cost | Scalability | Best For |
| Direct Exchange | Sub-250μs | High (per venue) | Low | HFT / Market Making |
| Hub-and-Spoke | 1–5ms | Medium | High | Buy-side / Asset Managers |
| FIX Gateway Layer | 2–10ms | Low–Medium | Very High | Multi-asset / Multi-system firms |
Infrastructure Requirements for Low-Latency FIX Implementation
FIX protocol implementation without the right infrastructure is like running Formula 1 software on consumer hardware. The protocol is fast. The infrastructure must match.
Low Latency Trading Infrastructure: Colocation, FPGA, Network
Low latency trading cloud infrastructure services are built on three pillars: physical proximity (colocation at exchange data centers like Equinix NY4 or the CME data center in Aurora, Illinois), hardware acceleration (FPGA or ASIC-based FIX engines that bypass the OS kernel), and optimized networking (kernel bypass via RDMA or DPDK, direct NIC-to-application paths).
For strategies requiring execution below 500μs, kernel bypass is mandatory. For institutional order management with less extreme latency needs, a well-tuned software FIX engine on dedicated bare metal at a co-location facility is sufficient.
#STAT CALLOUT: Using FPGA acceleration for FIX message parsing can reduce round-trip latency from ~2ms to under 250μs — an 8x improvement that translates directly to better fill rates in competitive markets.
High Availability, Failover, and Redundancy
Production FIX systems require N+1 redundancy at every layer: dual network paths, primary/standby FIX engine pairs, replicated message stores, and automatic failover with session continuity. Session handoffs during failover must maintain sequence number integrity or trigger a clean resync — not a gap that halts trading.
Design for the worst case: primary data center failure during peak trading hours. Your RTO (Recovery Time Objective) for FIX connectivity should be under 30 seconds. Achieving this requires automated failover, not manual intervention.
Observability and Monitoring with AI/ML Integration
Modern FIX monitoring goes beyond heartbeat checks. AI-driven cloud observability tools analyze message latency distributions, detect anomalous rejection patterns, and predict session degradation before it impacts execution. Key metrics to monitor in real time: Time-to-ACK per venue, rejection rate by message type, sequence gap frequency, and heartbeat response time.
Testing, Certification, and Production Readiness Checklist
Exchange certification is a hard prerequisite for production FIX connectivity. It is also where most implementation timelines slip. Build your certification plan into the project schedule from day one.
Simulation and Backtesting Environments
All major exchanges provide FIX simulation environments (UAT/CTE). Use them to validate every message type in your integration before submitting for certification. Simulate error conditions — invalid prices, duplicate ClOrdIDs, out-of-sequence messages — and verify your engine's behavior.
Exchange Certification Process
NYSE, NASDAQ, and CME each run structured certification programs. The process involves scripted test cases covering order types, cancel/replace flows, reject handling, and disconnection recovery. Allow 4–8 weeks for a typical certification cycle. Allocate engineering time for defect remediation — first-attempt pass rates are below 50% for new implementations.
Pre-Production Checklist
Before go-live, validate every item on this list:
- Session validation: All CompIDs, HeartBtInt, and message store settings confirmed
- Failover test: Primary engine failure → standby takes over within SLA
- Load test: Sustained message throughput at 120% of expected peak volume
- Gap recovery test: Simulate missed messages and confirm ResendRequest handling
- Compliance validation: All required fields populated per regulatory and venue spec
- Monitoring: All alerting thresholds set and tested
- Runbook: Operational procedures documented and reviewed with the trading desk
Security, Compliance, and Auditability in FIX Implementations
Implementing the FIX protocol requires more than just connectivity; it demands a robust framework to protect sensitive financial data and satisfy stringent regulatory requirements.
Here is a breakdown of the core pillars for securing and auditing FIX-based systems
Encryption and Secure Sessions — TLS and mTLS
FIX connections must be encrypted in transit. TLS 1.2 is the minimum; TLS 1.3 is the current standard. For institutional-grade deployments, mutual TLS (mTLS) is required — both sides present certificates, eliminating the risk of man-in-the-middle attacks on trade data. This is especially critical for FIX sessions carrying pre-trade compliance data or sensitive order information.
Regulatory Requirements: SEC and FINRA Context
In North America, FIX implementations must meet SEC Rule 15c3-5 (Market Access Rule) requirements for pre-trade risk controls. FINRA's OATS reporting and CAT (Consolidated Audit Trail) requirements mandate that all order events — including FIX messages — are captured with microsecond-level timestamps. Your FIX protocol integration services must include mechanisms for timestamping, logging, and regulatory reporting from day one.
Audit Trails and Trade Surveillance
Every FIX message must be logged with full content, timestamps, and session metadata. This log is your audit trail. It supports surveillance, incident investigation, and regulatory reporting. Immutable, append-only log stores with cryptographic integrity checks are best practice. Retention requirements in the US are a minimum of three years for order records.
#Note:- FIX message logs are regulatory artifacts. Under SEC and FINRA rules, they are required for compliance reporting and must be retained, protected, and available for audit.
Cost, Timeline, and Team Structure for FIX Protocol Implementation
The cost of FIX protocol implementation is one of the most underestimated line items in trading technology budgets. Here is a realistic breakdown.
Cost Breakdown: Infrastructure, Licensing, and Dev Effort
| Cost Component | Indicative Range | Key Variables |
| FIX Engine (Commercial License) | $50K–$500K/year | Vendor, message volume, venues |
| Infrastructure (Colocation + Hardware) | $100K–$1M+ | Latency tier, redundancy, region |
| Development & Integration | $150K–$600K | In-house vs. consulting, complexity |
| Exchange Certification | $20K–$80K per venue | Number of venues, first vs. re-cert |
| Ongoing Maintenance | $100K–$300K/year | Team size, number of connections |
Timeline by Complexity
- Simple single-venue FIX integration (e.g., one broker): 6–10 weeks
- Standard multi-venue buy-side implementation: 3–5 months
- Full custom FIX engine build with certification: 6–9 months
- Enterprise platform re-architecture: 9–18 months
Required Roles
- FIX Protocol Engineers (minimum 2, ideally with exchange-specific experience)
- QA Engineers with FIX simulation experience (minimum 1)
- DevOps/Infrastructure Engineer for low-latency environment setup
- Compliance/Regulatory Analyst for audit trail and reporting requirements
One way to reduce the cost of FIX protocol work: use managed FIX connectivity services for standard broker/exchange connections, reserving custom build effort for the proprietary layers where differentiation is possible.
Build vs. Buy: Choosing the Right FIX Implementation Strategy
This is the decision that most determines total cost, time-to-market, and long-term operational risk. There is no universal right answer. The right answer depends on four factors.
When to Build a Custom FIX Engine
Build when latency requirements demand kernel-bypass or FPGA-level optimization that commercial products cannot match. Build when your order flow has proprietary message formats or routing logic that no vendor supports. Build when you have the engineering talent and a long-term commitment to maintaining the engine.
When to Use FIX Protocol Integration Services
Use FIX protocol integration services when speed-to-market matters more than micro-optimization. When your differentiation is in strategy, not connectivity. When your team lacks deep FIX engineering expertise. When you are entering a new asset class or geography, you need certified connectivity quickly.
Hybrid Approach: The Best Practice Model
The most common model for established capital markets firms: a commercial FIX engine for standard venue connectivity, with custom application-layer logic for order routing, risk controls, and execution analytics. This balances time-to-market with flexibility.
Key Takeaways
| Factor | Build | Buy / Managed | Hybrid |
| Latency (sub-100μs) | Best | Limited | Good |
| Time to Market | 12–18 months | 1–3 months | 3–6 months |
| Upfront Cost | High | Low–Medium | Medium |
| Ongoing Maintenance | High | Low | Medium |
| Customization | Full | Limited | Moderate |
| Best For | HFT / Prop Trading | Buy-side / Mid-tier | Institutional Brokers |
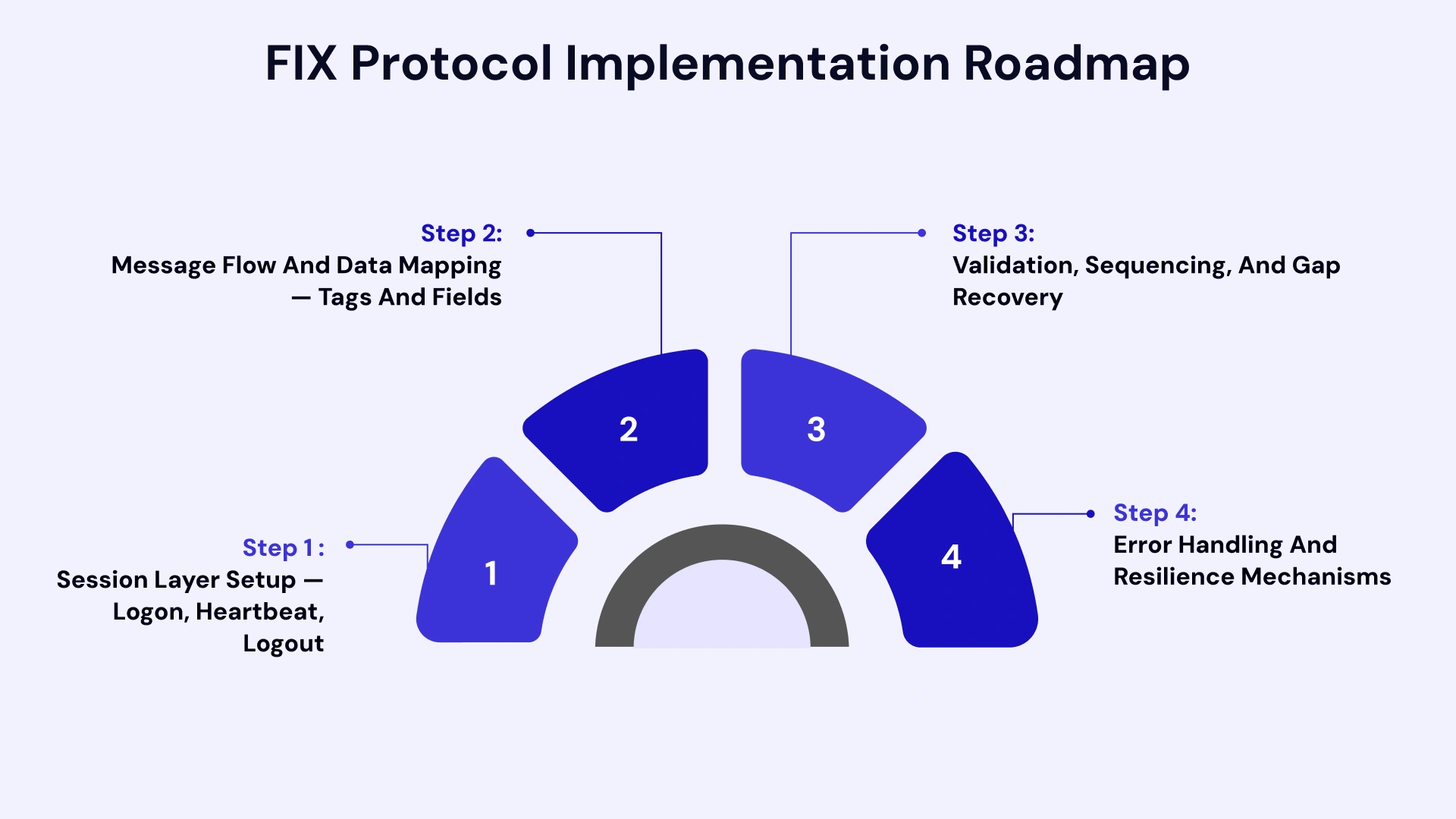
Common Architecture Mistakes in FIX Implementations
These are the errors that show up repeatedly in post-incident reviews and failed certifications:
1. Treating FIX as just an API: FIX is a session-driven, infrastructure-dependent connectivity layer. It requires persistent state, fault tolerance, and operational discipline that REST APIs do not.
2. Poor session management design: Embedding session logic inside business layer code creates rigid, hard-to-maintain systems. Keep the session layer isolated and replaceable.
3. No observability from day one: Many teams build FIX connectivity without real-time monitoring. By the time something breaks in production, the diagnostic window has closed.
4. Ignoring scalability in the initial design: Message volumes spike during volatility events. A FIX implementation that handles 10,000 messages per second in normal conditions may collapse at 50,000 during a market event. Load test to 2x expected peak.
5. Skipping the compliance layer: Post-trade reporting and audit logging are often deferred to phase two. They should be designed in from the start — retrofitting them is significantly more expensive.
The best-performing FIX implementations we have seen share one trait — they were designed by teams that understood both the protocol and the trading workflows it serves. FIX engineering without a trading context produces technically correct but operationally brittle systems.
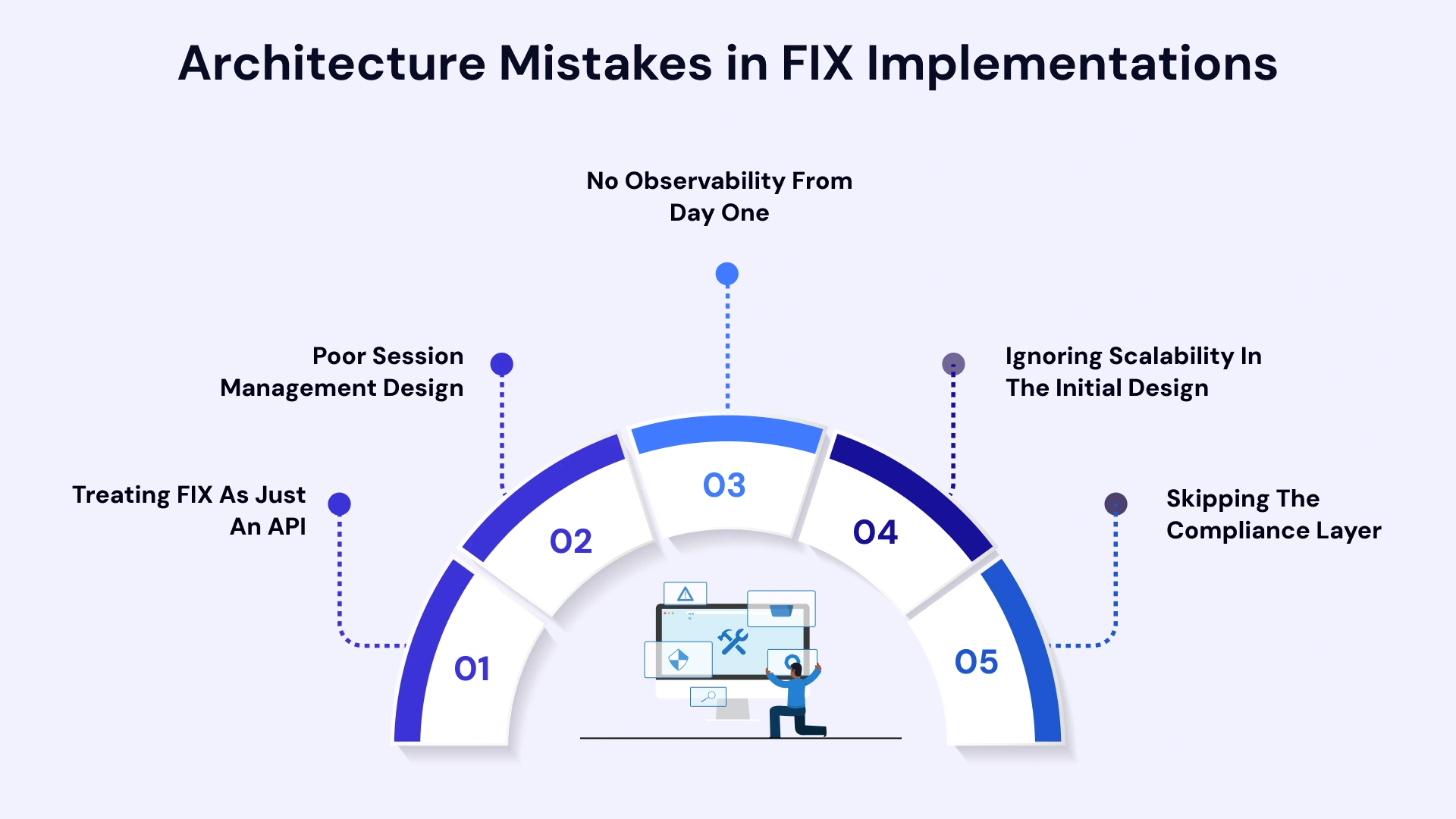
Future Trends in FIX and Trading Platform Architecture
Financial Information eXchange future trends point toward four major shifts that CTOs should be planning for now.
- FIX 5.0 and FIXP Adoption: FIX 5.0 separates the session layer from the application layer, enabling FIXP (FIX Performance) for high-performance environments. FIXP supports binary encoding and UDP transport — removing TCP head-of-line blocking limitations.
- FIX over QUIC: Early implementations are testing FIX over QUIC protocol to gain UDP-speed benefits with built-in reliability. This is particularly relevant for cross-geographic FIX connectivity where TCP latency is a ceiling.
- Event-Driven Architectures: Modern trading platform architecture is shifting toward event-driven microservices where FIX messages trigger downstream logic asynchronously. This improves throughput and fault isolation but requires careful sequencing guarantees.
- AI-Driven Execution Optimization: AI models are being integrated at the FIX gateway layer to predict execution quality, detect routing anomalies, and optimize order slicing in real time — turning the FIX layer from a dumb pipe into an intelligent execution surface.
Modernize Your Infrastructure with VLink Expertise
For CTOs and Heads of Technology managing complex trading environments, the gap between a working FIX implementation and a high-performance, scalable one often comes down to execution experience. VLink brings deep capital markets expertise across the full stack.
Our financial exchange solutions and trading platform modernization capabilities cover the end-to-end FIX lifecycle — from architecture design to exchange certification to production support. We work with custom trading platform development companies, broker-dealers, asset managers, and exchanges across North America.
Where VLink delivers value:
- Legacy System Modernization: We specialize in legacy system modernization services - migrating aging FIX implementations to microservices-based architectures without disrupting live trading operations. Our approach mirrors the best practice model: migrate trading platforms to microservices while maintaining certification continuity.
- Cloud and Infrastructure: Our cloud migration consulting services and cloud infrastructure services ensure your FIX environment is elastic, observable, and resilient. For latency-sensitive workloads, we provide low-latency trading infrastructure consulting to identify colocation and hardware acceleration strategies that match your strategy profile.
- Managed Cloud Services: For firms looking to reduce operational overhead, our managed cloud services cover FIX session monitoring, failover management, and infrastructure scaling — so your team focuses on strategy, not connectivity.
- Security and Compliance: As a trusted cybersecurity service provider for financial institutions, we implement Zero Trust architectures, mTLS for FIX sessions, and immutable audit logging that satisfies SEC and FINRA requirements.
- Custom Finance Software Solutions: Where off-the-shelf FIX products fall short, our finance software solutions team builds custom FIX engines, message transformation layers, and execution analytics platforms tuned to your specific needs.
We have helped firms reduce FIX maintenance costs by consolidating multi-broker connectivity into managed hubs, reducing round-trip latency through infrastructure re-architecture, achieving first-pass exchange certification, and building Trading platform modernization frameworks that scale across asset classes.
Conclusion
Trading platform architecture built on FIX protocol is a strategic asset. Done right, it enables institutional-grade execution, regulatory compliance, and the connectivity infrastructure needed to compete in modern capital markets.
The firms that win are not necessarily those with the fastest engines. They are the ones that treat FIX implementation as an architecture discipline — investing in the right infrastructure, getting certification right the first time, building observability from day one, and planning for scale before they need it.
Whether you are starting a new FIX protocol implementation or modernizing an existing trading stack, the steps outlined in this guide give you the architecture-first framework to do it at institutional standards.
Ready to build or scale? Contact us today to get started.

Global Delivery Manager, VLink Inc.
Shivisha Patel serves as the Global Delivery Manager at VLink Inc., bringing a wealth of experience in program delivery and management, particularly in the insurance and banking sectors. She has a robust technical background with deep expertise in WebSphere MQ, WTX, IIB, middleware, and enterprise system integration.








 Shivisha Patel
Shivisha Patel