Financial services firms are no longer asking if they need DevOps. They are asking how to implement it without triggering a regulatory crisis. The pressure is real and growing fast.
For CTOs and VP Infrastructure leaders in capital markets, these numbers signal one thing: the old model — build fast, audit later — is broken.
The new standard is compliance-first DevOps. This is not about slowing down delivery. It is about engineering delivery pipelines where DevOps financial services compliance is baked in at every stage — from the first line of code to production deployment.
This guide gives CTOs and infrastructure leads a practical implementation blueprint. Not theory. Not vendor pitches. A step-by-step model you can use to design, build, and run audit-ready CI/CD pipelines in regulated Capital Markets IT services environments.
What Does Compliance-First DevOps Mean in Financial Services?
Most organizations talk about DevOps in financial services as a delivery strategy. Compliance-first DevOps is something deeper. It is an architectural principle.
It means that every pipeline gate, every deployment trigger, every access control, and every log entry is designed to satisfy a regulatory requirement — not just a technical one.
From DevOps to DevSecOps to Compliance-as-Code
Traditional DevOps focused on speed and automation. DevSecOps added security tooling into the pipeline. Compliance-as-Code takes it further: it encodes regulatory rules — SEC 17a-4, FINRA, PCI DSS, SOX — directly into the pipeline as enforceable policy. If code violates a rule, the build fails. No manual review required.
Tools like Open Policy Agent (OPA) and HashiCorp Sentinel allow teams to write compliance requirements as machine-readable policies. This is how leading institutions are eliminating the gap between what auditors expect and what pipelines actually enforce.
But why do traditional DevOps models fail in Capital Markets?
Generic DevOps was designed for high-velocity consumer software. Capital markets operate under fundamentally different constraints: strict segregation of duties, mandatory change approval records, data residency rules, and real-time auditability.
A Tier-1 investment bank recently delayed a critical trading platform release by three weeks because the compliance team needed manual evidence collection for a SOX audit highlighting how similar inefficiencies can also impact fintech and blockchain projects that rely on cryptocurrency wallet development services, where automated compliance and security validation are essential to avoid costly delays.
Regulatory Landscape: What Your CI/CD Pipeline Must Satisfy
Before designing a pipeline, CTOs need to map the control requirements their CI/CD system must meet. In North America, the primary frameworks are:
- Core Frameworks
Framework | Regulator | Key CI/CD Impact |
PCI DSS v4.0 | PCI SSC | Access control, change management, audit logs for cardholder data systems |
SOX Section 404 | SEC / PCAOB | Segregation of duties, change authorization, audit trail retention |
SEC Rule 17a-4 | SEC | Immutable record retention, audit trail completeness |
FINRA Rules | FINRA | Supervisory systems, documented change controls |
GDPR (cross-border) | EU / State AGs | Data handling in pipelines, cross-border transfer controls |
Control Categories That Directly Impact DevOps
- Access Control (IAM): Who can trigger deployments, approve releases, and access production environments
- Change Management: Every code change must be logged, reviewed, and approved before production
- Data Protection: Pipelines must enforce encryption at rest and in transit for regulated data
- Auditability: Every action in the pipeline must produce a timestamped, immutable log entry
Understanding these requirements turns compliance from a constraint into a design specification. Your pipeline architecture becomes a regulatory control map.
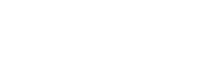
Why Standard CI/CD Pipelines Break in Regulated Environments
Most standard CI/CD implementations were not designed for capital markets. When financial firms try to adapt them, four structural problems emerge.
- Lack of Segregation of Duties (SoD)
Regulators require that the person who writes code cannot be the same person who approves and deploys it. Generic pipelines often allow developers to self-approve merges and trigger deployments. In a regulated environment, that is an immediate audit finding.
- Missing Audit Trails
Compliance dedicated teams need a complete, timestamped record of who changed what, when, why, and who approved it. Standard pipelines log build results. They do not log the full decision chain. Auditors want the decision chain.
- Manual Evidence Collection — The Audit Tax
On average, compliance teams in financial services spend 30% of their time collecting manual evidence for audits — screenshots, log exports, and approval emails. This is the audit tax. It is entirely avoidable with automated evidence pipelines.
- Tool Fragmentation
Most firms have separate tools for SAST, DAST, secrets scanning, IaC scanning, and deployment. None of these talk to each other by default. The result is alert fatigue, duplicate findings, and compliance gaps that only show up during an audit.
The Compliance Maturity Gap Model maps where most organizations sit:
Maturity Level | Description | Audit Readiness |
Level 1: Manual | Manual approvals, spreadsheet logs, email evidence chains | High risk — 3-6 weeks to prepare |
Level 2: Tool-based | Some SAST/DAST tools in place but disconnected | Medium risk — still manual evidence gaps |
Level 3: Policy-driven | Policy-as-Code in CI gates, automated access controls | Low risk — most evidence auto-generated |
Level 4: Audit-ready automation | Full continuous compliance — real-time dashboards, zero-touch production | Minimal risk — audit prep in hours, not weeks |
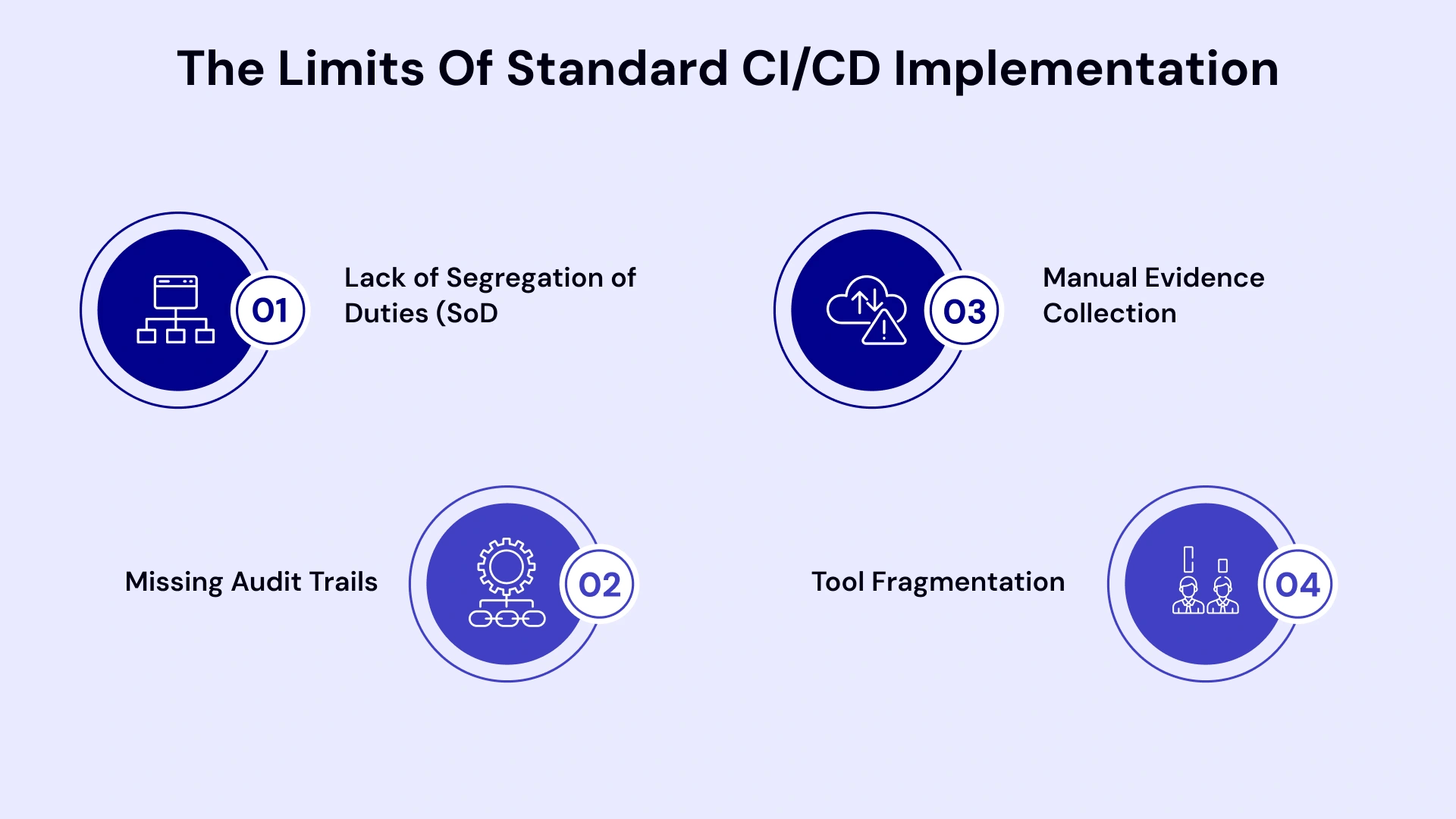
The Compliance-First CI/CD Architecture: Step-by-Step Blueprint
This is the core of the guide. Below is a five-stage architecture that embeds DevOps financial services compliance directly into the delivery CI/CD pipeline. Each stage has a specific control objective mapped to a regulatory requirement.
Stage 1: Pre-Commit — Shift-Left Governance
Compliance starts before the code is even pushed. IDE-level plugins — such as Spectral, git-secrets, or Talisman — scan for hardcoded credentials, non-compliant data patterns, and policy violations at the developer workstation. If a developer accidentally includes a private key or PII in a commit, it is caught before it ever enters the repository.
This is the cheapest place to fix a compliance problem. The cost of catching an issue here versus in production is roughly 100:1.
Stage 2: Continuous Integration — The Automated Auditor
Every commit triggers an automated compliance sweep. This includes:
- SAST (Static Application Security Testing): Checks source code for security vulnerabilities and coding standard violations
- SCA (Software Composition Analysis): Scans third-party libraries for known CVEs and license compliance
- Policy-as-Code Validation: OPA or Sentinel checks enforce FINRA, SOX, and PCI DSS rules as code — the build fails if any policy is violated
- Secret Scanning: Detects leaked credentials, API tokens, and cryptographic keys in the codebase
This stage functions as a regulatory gate. No code that violates a compliance rule can proceed to the next stage. All results are automatically logged to the audit evidence repository.
Stage 3: Environment Parity — IaC Governance
Using Infrastructure-as-Code (IaC) — Terraform, Ansible, or AWS CDK — ensures that the test environment is a bit-for-bit clone of production. This eliminates 'works in staging, fails in production' compliance failures.
Tools like Checkov or tfsec scan IaC templates themselves to ensure they do not provision non-compliant infrastructure (e.g., unencrypted databases, publicly exposed storage buckets, missing access logging).
Stage 4: Continuous Delivery — Dual Approval Gates
This is where Segregation of Duties is enforced at the pipeline level. No single individual can approve their own deployment. Two digital approvals are required:
- Technical Approval: Peer review sign-off from a second engineer confirming code quality and test coverage
- Regulatory Approval: Security or compliance officer digital sign-off confirming all policy gates have passed
This "Four-Eyes Principle" is enforced programmatically. The deployment pipeline is locked until both approvals are logged. The full approval chain — who approved, when, from which device, under which policy version — is automatically written to the immutable audit log.
Role-Based Access Control (RBAC) ensures that only authorized personnel can trigger each gate. Developers cannot approve their own work. Approvers cannot deploy without the technical gate passing first.
Stage 5: Continuous Monitoring — Drift Detection and Auto-Remediation
Compliance does not end at deployment. Production environments drift. Configurations change. Access permissions expand. Without continuous monitoring, a compliant deployment can become non-compliant within hours.
AI-driven observability tools — Datadog, AWS Config, Azure Policy — monitor production systems in real time for compliance drift. When drift is detected (e.g., a security group rule is modified, an encryption setting is disabled), the system either auto-remediates to the compliant state or triggers an alert with full remediation instructions.
This is the foundation of automated compliance monitoring at enterprise scale.
- Executive Summary
Pipeline Stage | Control Objective | Key Tools | Regulatory Mapping |
Pre-Commit | Prevent non-compliant code entry | git-secrets, Talisman, Spectral | PCI DSS 6.3 |
Continuous Integration | Automated policy and vulnerability checks | SAST, SCA, OPA, Checkov | SOX 404, FINRA |
Environment Parity | IaC governance and config compliance | Terraform, tfsec, Ansible | PCI DSS 6.4 |
Continuous Delivery | Dual approval, SoD enforcement | Jenkins, GitLab CI, Spinnaker + RBAC | SOX 302, SEC 17a-4 |
Continuous Monitoring | Drift detection, auto-remediation | AWS Config, Datadog, Azure Policy | PCI DSS 10, SOX 404 |
Embedding Security Automation in the Pipeline
Security automation is the engine that makes DevOps compliance scalable. Without it, every compliance check requires a human — and humans do not scale at the speed of modern CI/CD pipelines.
- SAST, DAST, and SCA Integration
These three tools work at different layers of the application stack:
- SAST analyzes source code without executing it. It catches insecure coding patterns, injection vulnerabilities, and compliance violations before the application is built.
- DAST (Dynamic Application Security Testing) tests the running application. It simulates an external attacker and identifies runtime vulnerabilities that SAST cannot see.
- SCA scans all third-party dependencies and open-source libraries for known CVEs, outdated versions, and licensing issues that could create compliance exposure.
Running all three in sequence in the CI stage creates overlapping coverage. No single tool catches everything. The combination does.
- Secrets and IaC Scanning
Secrets management is one of the most common compliance failure points. A single leaked API key or database credential can trigger a breach notification, an SEC disclosure requirement, and a PCI DSS audit finding simultaneously.
Tools like Vault by HashiCorp, AWS Secrets Manager, and Azure Key Vault ensure secrets are never stored in code or IaC templates. Scanning tools run at pre-commit and CI stages to catch any violations before they reach the repository.
For Azure DevOps financial services compliance environments, Microsoft Defender for DevOps provides integrated secrets scanning and IaC security assessment natively within Azure Pipelines — making it a strong choice for firms already on the Azure ecosystem.
- Risk-Based Alert Prioritization
The biggest operational challenge in DevSecOps is alert fatigue. A mid-size financial services firm can generate thousands of security findings per week across SAST, DAST, and SCA tools. Most of them are low severity. A handful require immediate action.
Risk-based prioritization uses severity scoring (CVSS scores), exploitability data, and asset criticality to surface only the findings that represent a material compliance or security risk. This is how DevOps compliance solutions scale without overwhelming engineering teams.
Audit-Ready by Design: Evidence Collection and Reporting
The biggest gap in most financial services DevOps implementations is not the tooling. It is the evidence. Auditors do not just want to know that controls exist. They want proof that the controls operated correctly, for every deployment, over the entire audit period.
- Continuous Evidence Generation
Every pipeline action — code scan, policy check, approval decision, deployment trigger — should automatically write a structured record to an evidence repository. This happens at machine speed, not human speed. The result is a complete, timestamped audit trail for every change deployed to production.
One leading capital markets firm reduced audit preparation time from three weeks to under two hours after implementing automated evidence collection across its CI/CD pipeline. The compliance team stopped spending time collecting evidence and started spending time reviewing it.
- Immutable Logs and Git as Source of Truth
Git commit history is already an immutable, timestamped record of every code change. When combined with pipeline logs, approval records, and scan results, the Git repository becomes the primary audit evidence source — one that auditors can query directly, reducing the time your team spends responding to audit requests.
For immutable log storage, financial institutions typically use tamper-evident logging services: AWS CloudTrail with S3 Object Lock, Azure Monitor with immutable storage, or purpose-built solutions like Splunk with WORM storage.
- Real-Time Compliance Dashboards
Rather than generating compliance reports for auditors on request, leading firms now provide read-only compliance dashboard access. Auditors can see the real-time state of every control — pass/fail rates, open findings, approval chain completeness, deployment frequency — without requiring any data exports from the engineering team.
This is the "Continuous Audit" model. It replaces the quarterly audit snapshot with a live feed of compliance data. For regulators, it demonstrates proactive control management. For CTOs, it eliminates the scramble that typically precedes every audit cycle.
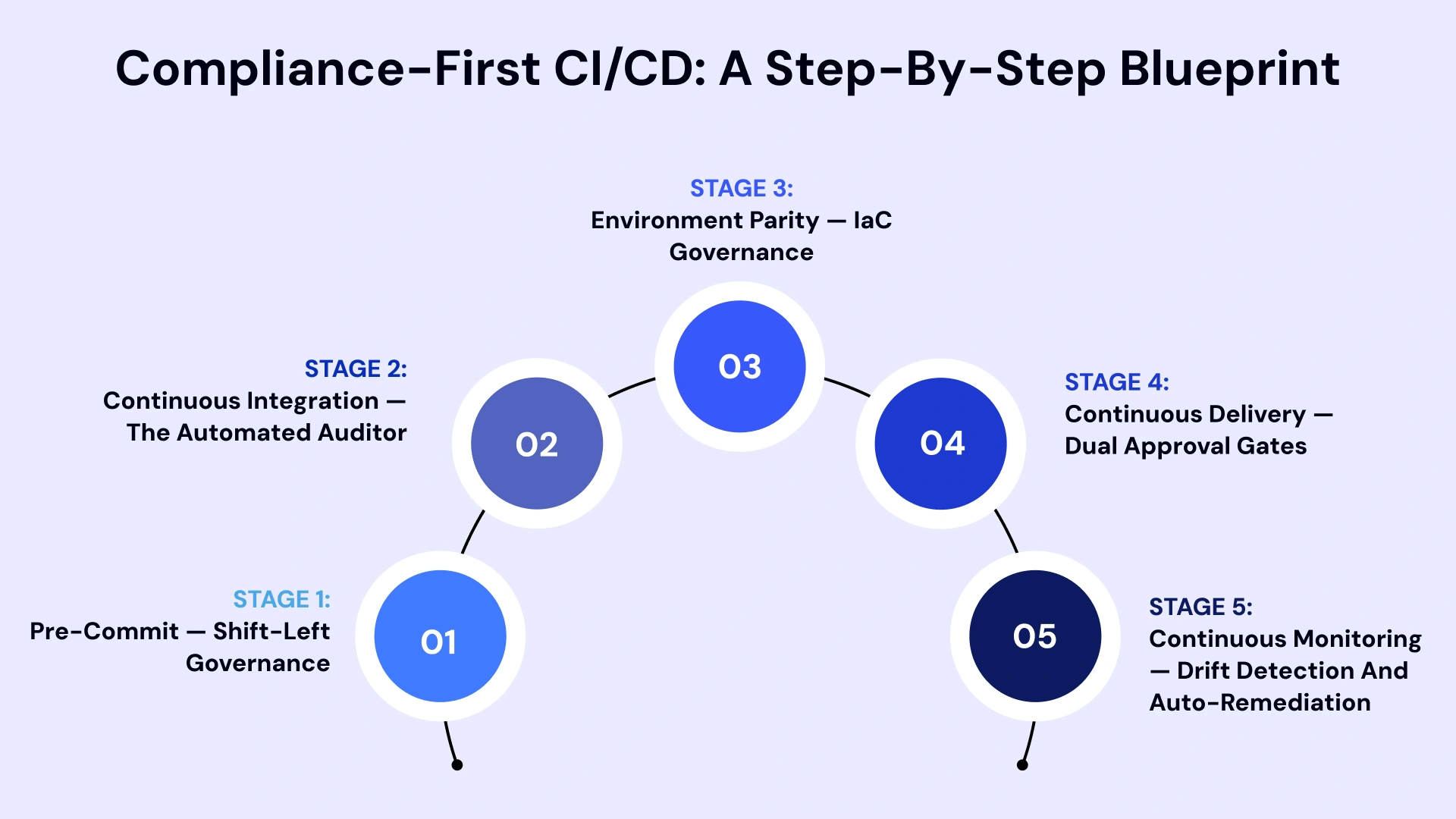
Governance Model: Segregation of Duties and Access Control
Governance is where DevOps in fintech applications most directly intersects with regulatory requirements. The three pillars of a compliant governance model are:
- Role-Based Access Control (RBAC)
Every action in the pipeline must be tied to a named individual with a defined role. Developers have access to development branches. Senior engineers can approve pull requests. Only designated release managers can trigger production deployments. Only security officers can override policy gates in documented emergency scenarios.
Access is provisioned on a least-privilege basis and reviewed quarterly. Any access change is logged automatically.
- Approval Workflows and Multi-Signature Releases
Digital approval workflows replace email chains and manual sign-off processes. Each approval is cryptographically tied to the approver's identity, the specific pipeline run, the policy version in effect, and the timestamp. This creates a non-repudiable record that satisfies SOX, PCI DSS, and FINRA change management requirements.
- Zero-Touch Production — The North Star Model
The most mature DevOps financial services environments are moving toward zero-touch production: no human has direct SSH or console access to production systems. All changes — including emergency patches — must go through the version-controlled pipeline with appropriate approvals.
#Note:- This model makes unauthorized changes mathematically difficult. It also means that every production change has a corresponding approved pipeline run — providing complete auditability with zero manual effort.
For high-frequency trading DevOps infrastructure, zero-touch production is particularly valuable. In trading environments, unplanned production changes carry both regulatory risk and market risk. A pipeline-enforced deployment model eliminates both.
Note: Businesses evaluating Governance Model: Segregation of Duties and Access Control should also consider DevOps use cases in fintech platforms to improve execution quality, scalability, and long-term operational resilience.
Decision Framework: How to Design Your Compliance-First Pipeline
Before investing in tooling or headcount, CTOs need to answer three foundational questions. The answers determine your optimal implementation path.
Decision Factor | Build Internally | Buy / License Tools | Partner with DevOps Consultants |
Internal DevOps team maturity | High — experienced DevSecOps team in place | Medium — team can configure and manage tools | Low to medium — team needs augmentation |
Regulatory complexity | Single-framework environments | Multi-framework with standard controls | Multi-framework with capital markets specifics |
Time-to-market pressure | 12+ month runway | 6-12 month runway | Under 6 months — accelerated implementation |
Audit readiness target | Long-term continuous improvement | Near-term compliance gaps | Immediate audit preparation required |
Key Questions for CTOs
- What is your current audit finding rate, and where are the most common gap areas?
- Does your team have experience writing Policy-as-Code in OPA or Sentinel?
- Can your existing pipeline tools (Jenkins, GitLab CI, Azure DevOps) be extended for compliance automation, or do you need to replace them?
- What is your target time to audit readiness — and what is the cost of missing that target?
The 90-Day Execution: Implementation Roadmap
This roadmap gives infrastructure leaders a clear execution path from assessment to audit-ready CI/CD. It is designed to deliver quick wins early while building toward a sustainable compliance-first operating model.
First 30 Days: Assessment and Quick Wins
- Conduct a CI/CD compliance gap assessment against your primary regulatory frameworks
- Implement pre-commit secrets scanning and basic SAST in existing pipelines (lowest-effort, highest-impact first step)
- Map current approval workflows and identify SoD gaps
- Establish baseline audit evidence collection for pipeline logs
- Define RBAC roles and begin access review of production systems
60 Days: Pipeline Automation and Controls
- Deploy Policy-as-Code in the CI stage using OPA or Sentinel
- Implement dual-approval gates in the CD pipeline with cryptographic sign-off
- Integrate IaC scanning (Checkov, tfsec) into environment provisioning workflows
- Connect pipeline evidence to the centralized compliance dashboard
- Conduct first tabletop audit exercise using automated evidence — identify remaining gaps
90 Days: Audit Readiness and Optimization
- Complete full pipeline coverage: SAST, DAST, SCA, secrets scanning, and IaC scanning are all active
- Launch a real-time compliance dashboard for internal and auditor access
- Implement continuous drift detection and auto-remediation in production
- Run internal mock audit using only automated evidence — measure time to compile
- Document all controls, ownership, and escalation paths in a Pipeline Governance Runbook
#Pro Tips:- Firms that follow this roadmap consistently report a reduction in audit preparation time from 3-6 weeks to under 48 hours by the end of the 90-day cycle.
Common Mistakes That Lead to Compliance Drift
Even well-designed pipelines drift out of compliance. Here are the three most common failure modes and how to prevent them.
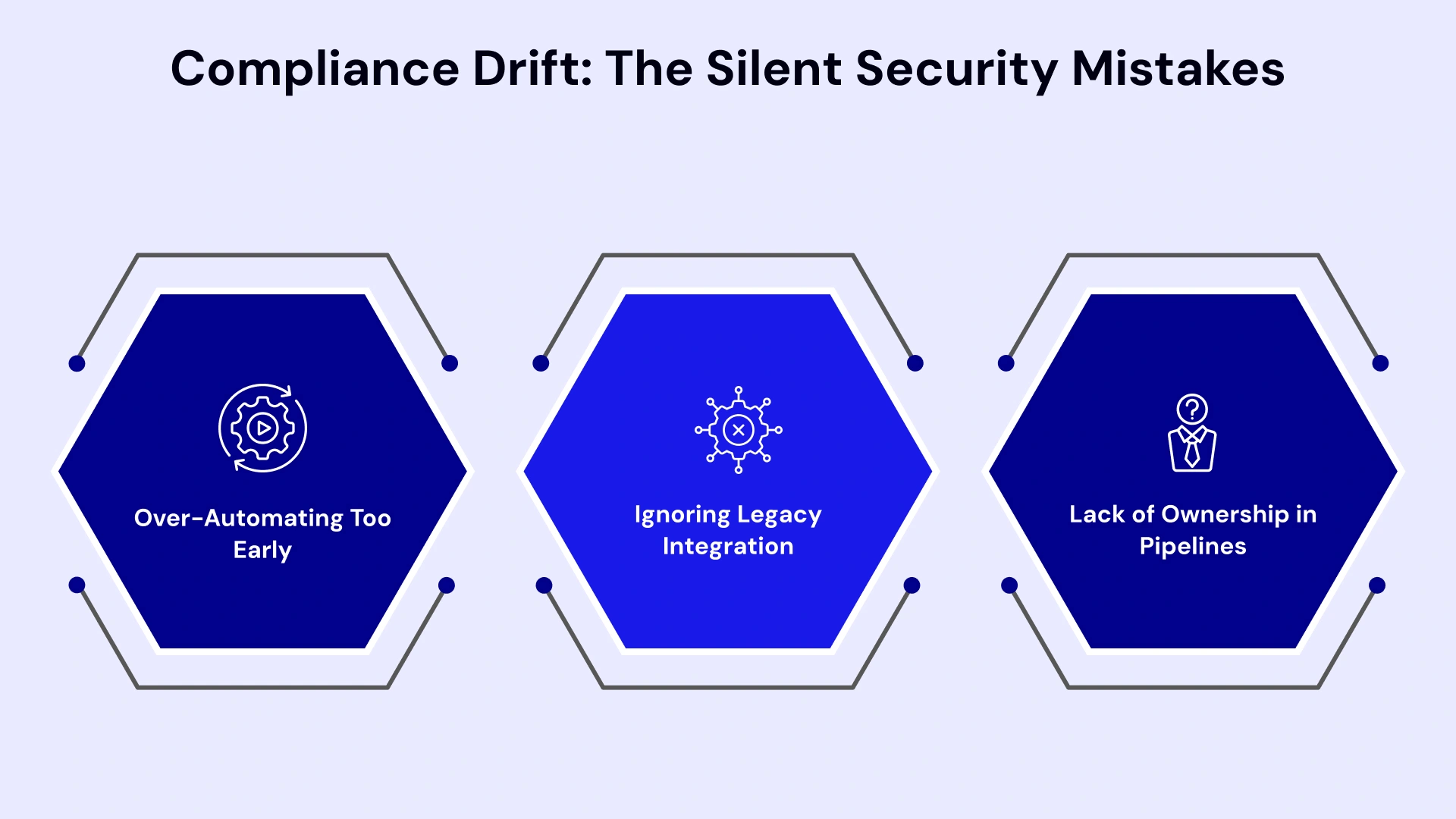
- Over-Automating Too Early
Teams that try to automate every compliance check in the first sprint often create brittle pipelines that generate hundreds of false positives. The result: developers bypass checks, alerts are ignored, and the pipeline becomes compliance theater rather than a real control.
Start with high-impact, low-complexity controls: secrets scanning, access management, and approval gate enforcement. Add complexity incrementally as the team builds confidence in the tooling.
- Ignoring Legacy Integration
As 44% of financial services professionals report significant difficulty integrating modern CI/CD pipelines with legacy mainframe and COBOL-based core systems. Ignoring legacy integration does not make it go away — it just means your compliance coverage has gaps exactly where your most sensitive data lives.
Use Change Data Capture (CDC) and API gateways to wrap legacy systems in a modern DevOps layer. This allows compliance controls to apply to both modern microservices and legacy cores through a consistent interface.
- Lack of Ownership in Pipelines
Every pipeline gate must have a named owner — a specific individual or team responsible for maintaining the control, reviewing alerts, and escalating issues. Pipelines without clear ownership drift because nobody is accountable for keeping them calibrated.
Create a Pipeline Governance Runbook that maps every gate to an owner, defines the response SLA for alerts, and specifies the escalation path for critical findings.
Real-World Examples: Capital Markets and Banking
Capital markets and banking are the twin pillars of the global financial system. While they both facilitate the flow of money from those who have it (savers/investors) to those who need it (borrowers/corporations), they operate through different mechanisms and institutions.
- Capital One: The AMI Bakery Model
Capital One moved from manual security scans that took two weeks to an API-driven "AMI Bakery" model — an automated pipeline that builds security-hardened machine images on a continuous basis. Developers can run their own vulnerability scans, remediate findings in real time, and deploy with 95% security assessment coverage. Manual scan time dropped from weeks to minutes.
- JPMorgan Chase: Compliance Automation at Scale
JPMorgan's COiN (Contract Intelligence) platform automated the review of over 12,000 legal documents annually. By integrating compliance verification into their DevOps workflow, they reduced 360,000 hours of manual legal review to seconds — with 100% coverage versus the 0.1% sample rate typical of manual reviews.
These examples demonstrate a consistent pattern: when compliance is embedded in the delivery pipeline rather than bolted on afterward, both speed and accuracy improve simultaneously.
- Goldman Sachs: The "Policy-as-Code" Revolution
Goldman Sachs transitioned from a "check-the-box" compliance culture to a Policy-as-Code framework within their Legend data platform. Previously, ensuring that data usage met strict global financial regulations required manual sign-offs and lengthy audits by compliance officers. By embedding these regulatory rules directly into the developer's environment, the system now automatically blocks non-compliant code or data queries before they ever reach production.
This transformed a process that used to take weeks of back-and-forth into an instantaneous, automated "green light," allowing the firm to deploy financial models faster while maintaining a 100% digital audit trail for regulators.
- Key Takeaways from These Pillars
These examples demonstrate a consistent pattern: when compliance is embedded in the delivery pipeline rather than bolted on afterward, both speed and accuracy improve simultaneously.
- Capital One solved the Infrastructure bottleneck (AMI Bakery).
- JPMorgan Chase solved the Document/Legal bottleneck (COiN).
- Goldman Sachs solved the Data/Policy bottleneck (Policy-as-Code).

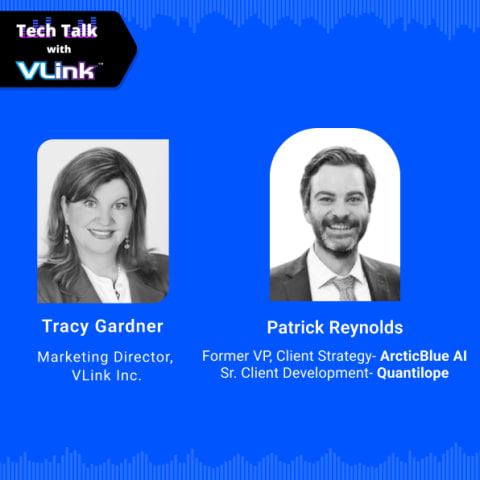
Leveraging VLink Expertise in DevOps Consulting Services
Designing and implementing a compliance-first CI/CD pipeline in a capital markets environment requires more than tooling knowledge. It requires a deep understanding of regulatory frameworks, financial services architecture, and the operational realities that CTOs and VP Infrastructure leaders face daily.
VLink's DevOps Consulting Services practice combines enterprise DevOps engineering with regulatory compliance expertise. Our teams have delivered compliant CI/CD implementations for capital markets, retail banking, and insurance clients — from initial assessment through full audit-ready production deployment.
What sets VLink apart:
- Capital markets-specific CI/CD design with PCI DSS, SOX, and FINRA controls embedded by default
- Financial Software Development Services that span the full delivery lifecycle — from architecture through ongoing pipeline optimization
- Rapid implementation — most clients achieve Level 3 compliance maturity within 90 days
- Dedicated DevOps services for banking with teams that understand both the technology and the regulatory environment
Whether you are building a compliance-first pipeline from scratch or remediating an existing one before an upcoming audit, VLink's Financial Software Development Services give you the expertise and the execution capacity to get there faster.
Conclusion: Compliance as a Competitive Advantage
The firms winning in capital markets today are not choosing between speed and compliance. They are using compliance as a design principle that makes their delivery pipelines faster, more reliable, and more auditable than those of their competitors.
DevOps for financial services done right means that your next audit is not a fire drill; it is a dashboard review. It means your engineering teams ship faster because compliance is handled by the pipeline, not by humans with spreadsheets. It means your CTO can walk into a board meeting and show real-time compliance metrics, not a slide deck built from manual data pulls.
The blueprint in this guide — five-stage pipeline architecture, Policy-as-Code enforcement, dual-approval gates, continuous evidence collection, and zero-touch production — gives capital markets leaders a concrete path to that outcome. Compliance-first CI/CD is not a constraint on DevOps. It is the most sophisticated form of it.
Ready to Build a Compliance-First DevOps Pipeline? VLink's DevOps Consulting Service and Financial Software Development Services teams deliver audit-ready CI/CD implementation for capital markets — from architecture to production, in under 90 days. Partner with VLink today!

Vice President, Strategy – VLink Inc.
Sambhavi Gopalakrishnan is the Vice President of Strategy at VLink Inc., bringing over a decade of experience in IT leadership, project implementation, and strategic growth. She possesses a strong foundation in technical project management and pre-sales, driving innovation and business transformation at VLink.







 Shivisha Patel
Shivisha Patel