When a traffic management system fails in a city of 3 million residents, it's not merely an IT incident—it's a civil safety crisis. As Gulf cities race toward their ambitious Vision 2030 and Centennial 2071 goals, they're building some of the world's most technologically advanced urban environments. But this hyper-connectivity creates what experts call the "Cyber-Physical Paradox": every connected device that improves city efficiency simultaneously expands the attack surface for malicious actors.
Gulf nations are adopting cloud-native security—cloud-native cybersecurity in the Gulf includes zero trust and DevSecOps.
For government technology leaders and enterprise CIOs across UAE and Saudi Arabia, the strategic imperative is clear: implementing cybersecurity best practices for smart cities isn't optional—it's foundational to national security. Organizations partnering with experienced cybersecurity services providers can accelerate their security posture while maintaining compliance with regional mandates. This guide delivers a Gulf-specific framework for securing IoT infrastructure while maintaining compliance with NCA and DESC mandates.
Why Securing Smart Cities in the Gulf Is Now a National Priority
The Gulf region has emerged as the world's most aggressive testbed for smart city innovation. From NEOM's cognitive city vision to Dubai's integrated urban services platform, these projects represent multi-billion-dollar investments in connected infrastructure. However, this transformation introduces systemic cyber risks that demand immediate attention from government and enterprise leaders. Understanding the landscape of software development in the Middle East provides essential context for the unique challenges facing regional deployments.
Hyperconnected Cities = Exponential Cyber Risk
Consider this scenario: A coordinated attack on Riyadh's traffic light system during rush hour. Within minutes, intersections across the city malfunction. Emergency vehicles cannot navigate gridlocked streets. The economic impact runs into millions, but the human cost—delayed ambulances, accidents at intersections—is incalculable. This isn't a theoretical exercise; similar incidents have occurred in cities worldwide, highlighting vulnerabilities that Gulf nations must address proactively.
The attack surface continues expanding as cities deploy additional connected infrastructure. Smart streetlights, environmental sensors, waste management systems, and public transportation networks all generate data streams that require protection. Each new device represents both an opportunity for improved city services and a potential entry point for malicious actors. This reality demands a fundamental shift in how security architectures are designed—moving from reactive patching to proactive, security-first infrastructure planning.
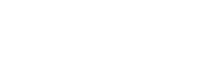
Regulatory Mandates: NCA (KSA) & DESC (UAE)
Non-compliance carries severe consequences. Beyond financial penalties, organizations face operational restrictions, reputational damage, and potential exclusion from government contracts. The message from regulators is unambiguous: continuous audit readiness is the new baseline, not periodic compliance checks. The regulatory framework continues evolving, with new guidelines addressing emerging technologies including AI-driven security systems and quantum-resistant encryption requirements.
Organizations leveraging comprehensive cybersecurity services can streamline compliance through automated governance, risk, and compliance (GRC) platforms that map technical controls directly to NCA and DESC requirements. These platforms reduce the manual burden of compliance documentation while ensuring continuous monitoring against regulatory standards.
Core Cybersecurity Challenges Facing UAE and Saudi Smart Cities
Understanding the specific pain points facing Gulf smart city projects is essential for developing targeted solutions. Three interconnected challenges dominate the landscape, each requiring distinct strategic responses. Addressing these challenges requires expertise in both AI development services and operational technology security—a combination that few organizations possess internally.
Fragmented IoT Ecosystems (Vendor Sprawl)
A typical Gulf municipality might deploy traffic cameras from one vendor, environmental sensors from another, street lighting systems from a third, and public safety equipment from yet another supplier. This vendor sprawl creates a patchwork of security protocols, firmware update schedules, and authentication mechanisms that's nearly impossible to manage holistically. The complexity multiplies when legacy systems from earlier smart city phases must integrate with newer deployments.
The consequence is weak visibility. Security teams cannot maintain consistent oversight when each vendor uses proprietary management interfaces. Attackers exploit these gaps—compromising a single vendor's devices can provide lateral movement opportunities across the entire city network. The challenge intensifies when considering that many vendors prioritize functionality over security, shipping devices with default credentials and minimal encryption capabilities.
Legacy OT Meeting Modern IoT
Gulf cities face a unique challenge: integrating decades-old operational technology with modern IoT infrastructure. SCADA systems controlling water treatment plants, legacy turbines in power generation facilities, and industrial control systems in utilities were never designed for internet connectivity. Yet smart city initiatives require these systems to communicate with cloud platforms and mobile interfaces.
These legacy systems cannot be taken offline for security patches without disrupting essential services. Traditional vulnerability management approaches fail when confronting 20-year-old industrial equipment now connected to modern networks. Organizations must adopt specialized approaches including virtual patching, network segmentation, and unidirectional gateways to protect these critical assets without operational disruption.
Thousands of Unmanaged IoT Devices
"You cannot secure what you cannot see." This fundamental security principle highlights the critical gap in most smart city deployments. Shadow IoT devices connect to city networks daily—unauthorized sensors, personal devices, contractor equipment—each representing an unmanaged entry point for attackers.
Without comprehensive asset discovery, security teams operate blind. Research indicates that organizations deploying AI-driven asset discovery tools can auto-detect every IP-connected asset, classify them by function, and assign risk scores—transforming visibility from a liability into a strategic advantage. Enterprises leveraging machine learning development services can build custom detection models trained on their specific network patterns.
Smart City Cybersecurity Challenges vs. Strategic Solutions
| Challenge | Root Cause | Gulf-Specific Solution |
| Legacy OT vs. Modern IoT | Industrial systems never built for internet connectivity | Data Diodes + Virtual Patching |
| Regulatory Compliance Pressure | Complex NCA/DESC frameworks with heavy penalties | Automated GRC Platforms |
| Fragmented Vendor Ecosystem | Multiple vendors with inconsistent security protocols | Zero Trust + mTLS Authentication |
| Lack of Visibility | Shadow IoT devices connecting daily | AI-Driven Asset Discovery |
| Skills Gap | Shortage of OT/IoT security specialists | Managed Security Services + Training |
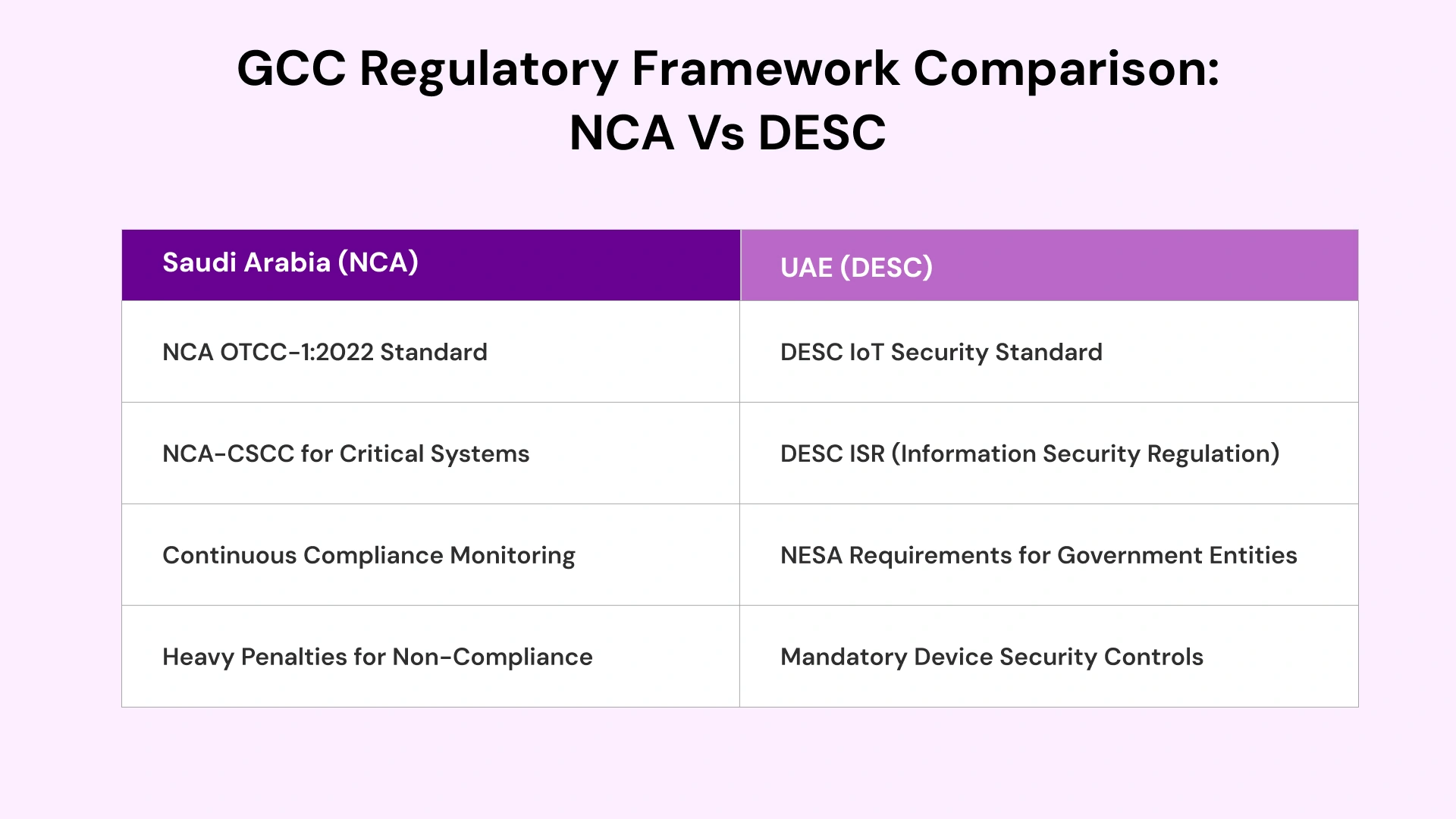
The Gulf Smart City Cybersecurity Framework (3-Phase Model)
Competing effectively in the Gulf smart city landscape requires a structured approach that addresses regional compliance requirements while delivering operational security. This three-phase model aligns with NCA OTCC-1:2022 and DESC IoT Security Standard, providing a clear roadmap for implementation that integrates with digital transformation services strategies.
Phase 1: Discovery & Governance — Establishing Digital Control
The foundation of any effective cybersecurity program is comprehensive visibility. This phase establishes the baseline for all subsequent security activities and typically requires 60-90 days for initial completion in medium-scale deployments.
Asset Census: Deploy passive listeners to map the entire IT/OT/IoT estate without disrupting operations. Every connected device—from traffic sensors to HVAC systems—must be catalogued with its network position, firmware version, and communication patterns. Modern discovery tools leverage machine learning to classify device types automatically, reducing manual effort by up to 80%.
Regulatory Mapping: Categorize assets based on criticality. Critical Infrastructure (power grids, water treatment) demands stricter controls than Public Wi-Fi networks. This categorization determines which NCA/DESC controls apply to each asset class and informs resource allocation decisions.
Vendor Risk Assessment: Enforce a "Secure Supply Chain" policy. Vendors must demonstrate their devices meet DESC IoT Security Standard before onboarding. This applies to hardware manufacturers, software providers, and system integrators alike.
Decision Framework — Criticality × Exposure Matrix: Prioritize assets by combining their operational importance (criticality) with their network accessibility (exposure). High-criticality, high-exposure assets demand immediate hardening; low-criticality, low-exposure assets can follow standard timelines.
Phase 2: Architecture & Hardening — Creating Secure-by-Design Cities
With visibility established, Phase 2 focuses on building architectural defenses that assume breach attempts will occur. This isn't pessimism—it's operational realism informed by threat intelligence and industry best practices.
Identity First: Assign a "Digital Identity" to every device using Public Key Infrastructure (PKI). Devices without a valid certificate are instantly rejected from the network. This eliminates rogue device spoofing—a common attack vector in smart city environments.
Micro-Segmentation: Divide the city network into isolated "zones" by function: Traffic Zone, Energy Zone, Public Services Zone. If a hacker breaches a streetlamp, they cannot jump to the power grid. This containment strategy limits blast radius from any successful attack. Organizations utilizing cloud infrastructure services can implement software-defined segmentation across hybrid environments.
Cryptographic Agility: Smart city infrastructure is built to last 15-20 years. Current encryption standards may not survive quantum computing advances. Transition to quantum-ready encryption standards now, protecting long-lifespan assets from "Harvest Now, Decrypt Later" attacks where adversaries collect encrypted data today for future decryption.
Decision Framework — Zero-Trust for IoT Maturity Ladder:
| Level | Capability |
| Level 1 | Device authentication only |
| Level 2 | Device + User authentication with role-based access |
| Level 3 | Continuous verification + behavioral analytics |
| Level 4 | Adaptive trust scoring + automated threat response |
Phase 3: Monitoring & Response — Building a Cyber-Resilient City
The final phase acknowledges a fundamental truth: perfect prevention is impossible. The metric for success isn't "Did we stop the attack?" but "How fast did we restore the traffic lights?" Resilience-focused strategies prioritize detection speed and recovery capabilities.
Converged SOC: Establish a Security Operations Center that monitors both IT and OT alerts in a single pane of glass. Traditional IT-only SOCs miss critical indicators from operational technology systems. Converged monitoring catches threats that span both environments. Teams should be staffed with analysts who understand both network protocols and industrial control system behaviors.
AI Anomaly Detection: Use AI to learn "normal" city behavior—water pressure patterns at 2 AM, traffic flow during rush hour, power consumption profiles. When pressure spikes abnormally or traffic patterns deviate without explanation, the system auto-alerts security teams to potential cyber-physical attacks. Organizations investing in AI development services gain custom detection models tailored to their specific infrastructure patterns.
Resilience Drills: Conduct "Cyber Fire Drills"—simulated ransomware attacks on city infrastructure to test recovery times. These exercises reveal gaps in incident response procedures before real attacks exploit them. Document lessons learned and update response playbooks accordingly.
Story: A Gulf utility operator detected unusual data flows from a water treatment sensor during high-load hours. Their converged SOC identified the anomaly within minutes—a compromised firmware update attempting to exfiltrate operational data. Automated containment isolated the affected segment while operations continued uninterrupted. The breach was neutralized in under 30 minutes with zero service impact—demonstrating the value of integrated monitoring and rapid response capabilities.
IoT Security Best Practices for Smart Cities (Gulf-Specific)
Implementing cybersecurity best practices for smart cities requires adapting global standards to Gulf-specific regulatory requirements and operational contexts. These five practices address the most critical vulnerabilities while maintaining compliance with NCA and DESC mandates.
1. Implement Zero-Trust for IoT/OT Networks
Zero-Trust operates on a simple principle: assume every device is compromised until proven otherwise. For Gulf smart cities, this means implementing Mutual TLS (mTLS) where both the device and server authenticate each other before any data exchange. This bidirectional verification eliminates man-in-the-middle attacks that plague traditional authentication models.
This approach prevents rogue devices from spoofing legitimate sensors—a critical concern when vendor sprawl means multiple device types from different manufacturers share the same network. The zero-trust model extends beyond initial authentication to continuous verification throughout each session, ensuring that compromised credentials cannot be reused for extended access.
2. Enforce Strong Device Identity & Secure Onboarding
Every IoT device entering the city network must have a cryptographically verifiable identity. This requires certificate-based authentication with regular rotation schedules—typically every 90 days for high-risk devices, annually for low-risk assets. Hardware Security Modules (HSMs) should protect private keys for critical infrastructure components.
Vendor attestation is equally critical. Before any device connects to city infrastructure, the vendor must certify its security posture, firmware integrity, and compliance with DESC IoT Security Standard. This shifts liability and ensures supply chain security from the first connection. Organizations should maintain a "Trusted Vendor Registry" that tracks attestation status for all approved suppliers.
3. Micro-Segment All Smart City Zones
Network segmentation isn't optional—it's the primary containment mechanism against lateral movement. Create strict isolation between traffic management systems, utility networks, public Wi-Fi, and administrative systems. Each zone should operate as an independent security domain with explicit policies governing inter-zone communication.
For legacy OT systems that cannot be patched, implement Data Diodes—hardware-enforced unidirectional gateways. The OT network sends data out to monitoring systems but physically cannot receive signals in, neutralizing remote tampering risks entirely. Organizations implementing DevOps services can automate network policy deployment and configuration management across segmented environments.
4. Continuous Threat Detection Using AI + Behavior Analytics
Static signature-based detection fails against novel threats. Modern smart city security requires AI-driven behavioral analytics that establish baseline patterns and flag deviations in real-time. These systems learn what "normal" looks like for each device type and alert when behavior deviates from established patterns.
This approach is particularly effective against insider threats—the 70% risk factor identified for Middle East organizations. When an authorized user's behavior deviates from established patterns, the system triggers investigation before damage occurs. Passive scanning tools that don't disrupt operations are essential for maintaining 24/7 detection without impacting city services. Integration with artificial intelligence in digital transformation strategies accelerates detection capabilities.
5. Build a Sovereign Cloud Strategy for City Data
Data sovereignty is emerging as a security control, not just a compliance requirement. KSA and UAE are tightening regulations on where smart city data resides. Citizen movement patterns, utility consumption data, and public safety information cannot leave national borders without explicit authorization and appropriate safeguards.
Sovereign Cloud adoption ensures smart city data remains within jurisdictional control while maintaining the scalability benefits of cloud infrastructure. This trend will accelerate through 2026 as regulations mature and enforcement increases. Organizations should evaluate local data center options and hybrid cloud architectures that maintain data residency while enabling global collaboration where appropriate.
Real-World Examples: How Gulf Cities Are Securing Smart Infrastructure
These case studies demonstrate practical implementation of cybersecurity best practices for smart cities in Gulf contexts. While specific client details remain confidential, the technical approaches and outcomes reflect real deployments across the region.
Case Study: "Cognitive City" in Saudi Arabia (NEOM-style)
Context: A mega-project building a city from scratch with millions of autonomous sensors monitoring everything from air quality to pedestrian flow. The project scope demanded security architecture capable of scaling from initial deployment to full city operations—a 10x growth trajectory.
Challenge: Securing millions of sensors without creating data backhauling bottlenecks that would slow real-time city operations. Traditional centralized security models would introduce unacceptable latency for time-sensitive applications like autonomous transportation and emergency response.
Solution: Implemented a Distributed Cloud Security model. Instead of sending all data to a central server for security inspection, security policies are enforced at the "Edge"—on the device and gateway level. Each sensor cluster processes security decisions locally, only escalating anomalies to central SOC. This architecture mirrors approaches used in manufacturing software development for industrial IoT security.
Result: 40% reduction in data latency while maintaining strict NCA-CSCC (Critical Systems Cybersecurity Controls) compliance. Security didn't slow the city—it enabled faster operations through reduced network congestion and more efficient threat processing.
Case Study: Dubai Utility Provider (DEWA-style)
Context: A major utility managing water and electricity for millions of residents, operating critical infrastructure that blends legacy SCADA systems from the 1990s with modern smart meter deployments and renewable energy management platforms.
Challenge: Converging 20-year-old OT turbines with new IoT smart meters while preventing ransomware attacks that could disable essential services. The utility could not afford any downtime for security upgrades—service continuity was non-negotiable.
Solution: Deployed Unidirectional Gateways (Data Diodes) at all IT/OT boundaries. The OT network sends operational data out to the billing system (IT) but physically cannot receive signals in. Combined with virtual patching for legacy systems that cannot be taken offline, and implemented network monitoring approaches similar to those used in telecom software development for critical infrastructure protection.
Result: Achieved 100% compliance with DESC ISR (Information Security Regulation) and prevented 3 attempted ransomware breaches in 2024. Zero service disruption despite active threat targeting—demonstrating that robust security can coexist with operational continuity.
People Also Ask (PAA) Answers - Gulf-Focused
What are the biggest cybersecurity challenges in smart cities?
Gulf smart cities face three primary challenges: fragmented IoT ecosystems from multiple vendors creating visibility gaps, legacy OT systems never designed for internet connectivity now integrated with modern networks, and regulatory compliance pressure from NCA (Saudi) and DESC (UAE) mandates requiring continuous audit readiness. Additionally, the skills gap for OT/IoT security specialists compounds these technical challenges.
How do you secure IoT devices in a smart city?
Secure smart city IoT through Zero-Trust architecture with mTLS authentication, PKI-based device identity management, network micro-segmentation isolating critical systems, AI-driven anomaly detection for behavioral monitoring, and sovereign cloud strategies ensuring data residency compliance with GCC regulations. Regular firmware updates and vendor attestation complete the security lifecycle.
What cyber threats do Gulf smart cities face?
Gulf smart cities face targeted ransomware against critical infrastructure, insider threats (70% of regional risk), nation-state actors targeting strategic assets, supply chain compromises through vendor devices, and "Harvest Now, Decrypt Later" attacks collecting encrypted data for future quantum decryption. Social engineering targeting city employees remains a persistent vector for initial access.
Which frameworks guide smart city security in UAE & Saudi Arabia?
UAE follows DESC IoT Security Standard and NESA requirements for government entities. Saudi Arabia mandates NCA OTCC-1:2022 for operational technology and NCA-CSCC for critical systems. Both countries require continuous compliance monitoring with significant penalties for non-adherence. International standards like IEC 62443 provide supplementary guidance for industrial control systems.
Decision Framework for GCC Cybersecurity Leaders
Use this Gulf Smart City Cyber Readiness Scorecard to evaluate your organization's security posture. Score each dimension 1-5, with recommended actions based on results. This assessment should be conducted quarterly to track progress and identify emerging gaps.
| Dimension | Score (1-5) | If Score <3, Next Step |
| Visibility | ___/5 | Deploy AI-driven asset discovery |
| Identity & Access | ___/5 | Implement PKI + certificate rotation |
| Segmentation | ___/5 | Micro-segment by utility zone |
| Monitoring | ___/5 | Establish converged IT/OT SOC |
| Vendor Compliance | ___/5 | Enforce supply chain attestation |
| Resilience | ___/5 | Conduct quarterly cyber fire drills |
Scoring Interpretation: Total 25-30 = Advanced readiness; 18-24 = Moderate gaps requiring attention; Below 18 = Significant vulnerabilities demanding immediate action.
The Road Ahead: 2025-2026 Smart City Security Trends in GCC
Strategic leaders must anticipate emerging trends shaping Gulf smart city security over the next 18 months. These trends will define investment priorities and capability requirements for forward-thinking organizations.
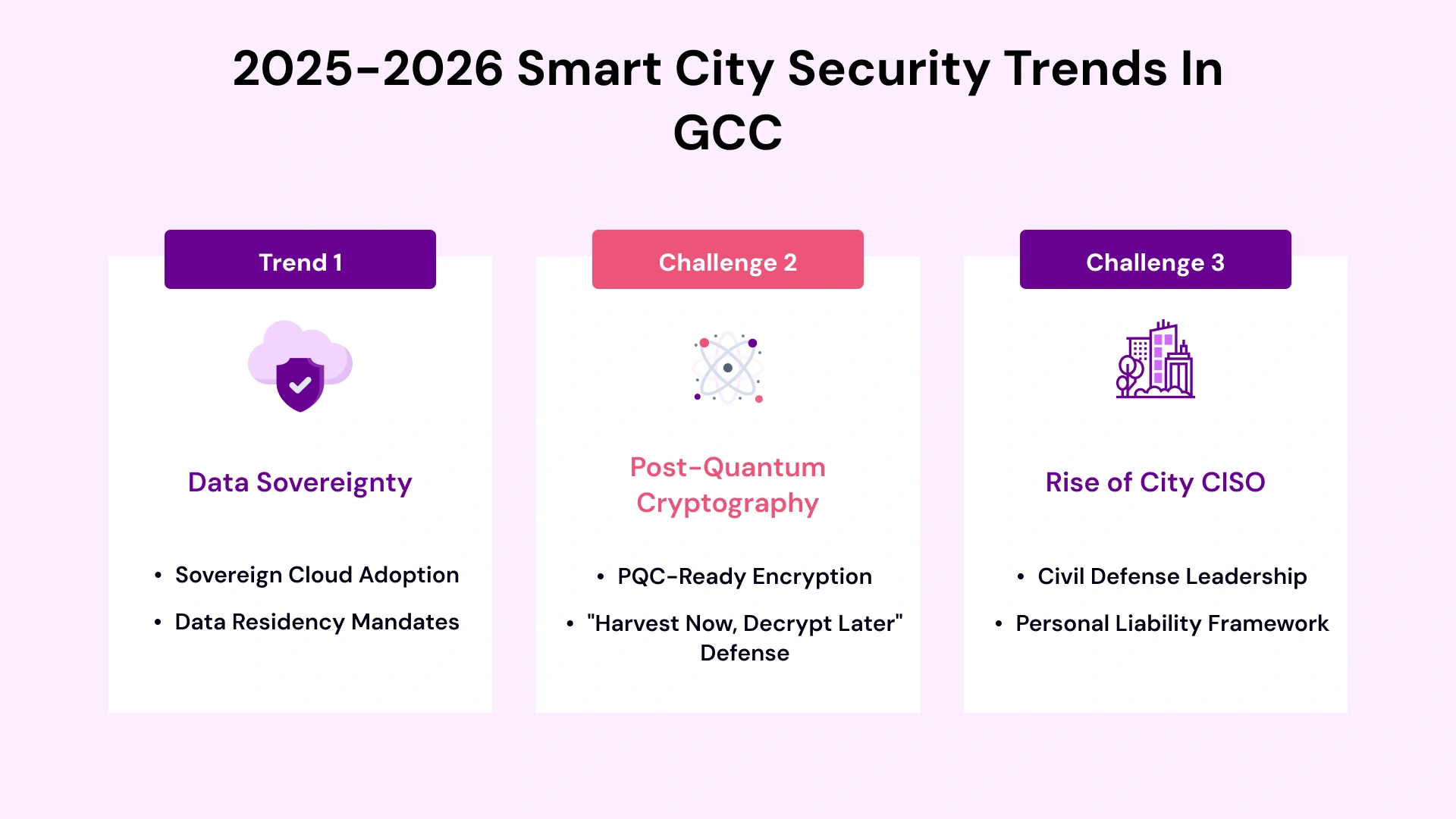
Data Sovereignty as Security Control: KSA and UAE regulations will increasingly mandate that smart city data—citizen movement patterns, utility consumption, public safety footage—remains within national borders. Sovereign Cloud adoption shifts from compliance checkbox to strategic security architecture. This trend accelerates the growth of regional data center capacity and local cloud service providers.
The Rise of the City CISO: This role evolves from technical director to Civil Defense Leader with legal accountability for city uptime and safety. Expect regulatory frameworks to codify personal liability for cybersecurity failures affecting critical infrastructure. The City CISO will coordinate across municipal departments, private sector operators, and federal agencies.
AI-Driven Threat Intelligence: Machine learning models will process threat feeds from global sources, correlating indicators with local infrastructure patterns to predict attack vectors before they materialize. Organizations investing in AI and ML for digital transformation will gain predictive capabilities that outpace traditional reactive approaches.
Conclusion - Securing the Gulf's Smart City Future Requires Resilience, Not Perimeters
The era of "unhackable" cities is a myth. Gulf smart city leaders must abandon the illusion of perfect perimeter defense and embrace a resilience-first mindset. The metric for success isn't whether an attack occurred—it's how quickly city services resumed normal operations and how effectively the incident was contained.
Under NCA and DESC regulations, the operator holds liability for security failures—not the vendor. Regulatory risk cannot be outsourced. This reality demands proactive investment in cybersecurity best practices for smart cities: comprehensive asset visibility, Zero-Trust architectures, micro-segmentation, AI-driven threat detection, and continuous compliance monitoring. Organizations must build security capabilities internally while leveraging experienced partners for specialized expertise.
Security is no longer about walls. It's about building an immune system that detects, contains, and recovers from threats while the city continues serving its citizens. The Gulf's smart city ambitions deserve security strategies equally ambitious—and equally forward-looking. By implementing the framework and best practices outlined in this guide, organizations can transform cybersecurity from a compliance burden into a competitive advantage that enables innovation rather than constraining it.

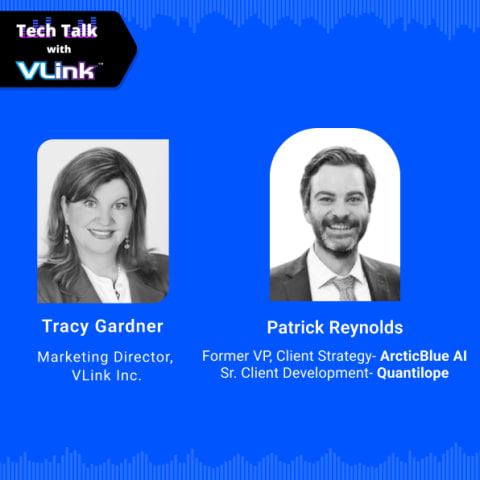
Vice President, Strategy – VLink Inc.
Sambhavi Gopalakrishnan is the Vice President of Strategy at VLink Inc., bringing over a decade of experience in IT leadership, project implementation, and strategic growth. She possesses a strong foundation in technical project management and pre-sales, driving innovation and business transformation at VLink.








 Shivisha Patel
Shivisha Patel