The cybersecurity threat surface for North American financial institutions has never been more complex. In 2026, three forces are converging simultaneously: the industrialization of AI-enabled attacks, a tightening regulatory environment demanding near-real-time incident disclosure, and systemic SaaS concentration risk that can cascade into sector-wide contagion.
Consider the numbers:
Key themes shaping 2026:
- AI operates on both sides of the attack surface — as attacker and defender
- Regulatory hyper-compliance is compressing disclosure timelines from days to hours
- Identity is the only remaining perimeter in a cloud-first, API-driven banking model
- Post-quantum cryptography migration is no longer optional — it is a board-level risk
For CISOs and CTOs in 2026, financial services cybersecurity trends dictate a shift from simple threat blocking to proven operational continuity. Demonstrating resilience during active, autonomous attacks is no longer just a security goal—it is a critical business metric for boards, regulators, and customers alike.
Why Cyber Risk Is Peaking for North American Financial Institutions
Financial services remain the most targeted sector globally. In 2025, the World Economic Forum's Global Cybersecurity Outlook flagged the sector's growing 'Cyber Equity Gap': large Tier 1 banks are hardening, while credit unions, regional banks, and fintechs are becoming the primary entry points for systemic attacks.
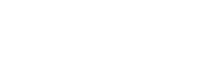
The Triple Threat Convergence
Three macro-forces are compressing at the same moment:
- AI-Enabled Autonomous Attacks: Threat actors now deploy AI to orchestrate phishing campaigns at an industrial scale, generate synthetic identities that pass biometric KYC, and automate lateral movement inside cloud environments. The R&D cost for attackers has collapsed.
- Quantum-Readiness Pressure: 'Harvest Now, Decrypt Later' (HNDL) attacks are actively accumulating encrypted financial data today, with the intent to decrypt when quantum computers reach cryptographic relevance (estimated 2029-2032). 45% of North American FSIs have begun post-quantum cryptography (PQC) migration — but 55% have not. (NIST PQC Standardization Timeline, 2024)
- SaaS Ecosystem Systemic Risk: The average financial institution now relies on 130+ SaaS applications. A single vendor failure — whether a cloud provider outage or a supply chain compromise — can trigger cascading failure across payments, lending, and compliance workflows.
The Financial and Reputational Impact of Breaches in 2026
The stakes extend well beyond direct breach costs. North American FSIs facing a material cyber incident in 2026 confront:
| Impact Category | 2026 Reality | Key Driver |
| Average Breach Cost | $6.4M+ | Cloud forensics, regulatory fines, legal fees |
| SEC Disclosure Deadline | 4 business days | 2023 SEC Cyber Disclosure Rule (material incidents) |
| Regulatory Penalty Range | Up to $250M+ | NYDFS violations, OCC enforcement actions |
| Customer Churn Risk | 18-25% post-breach | Trust erosion, especially in retail and wealth |
| Cyber Insurance Renewal | Now requires live EDR telemetry | Insurers demanding real-time posture data |
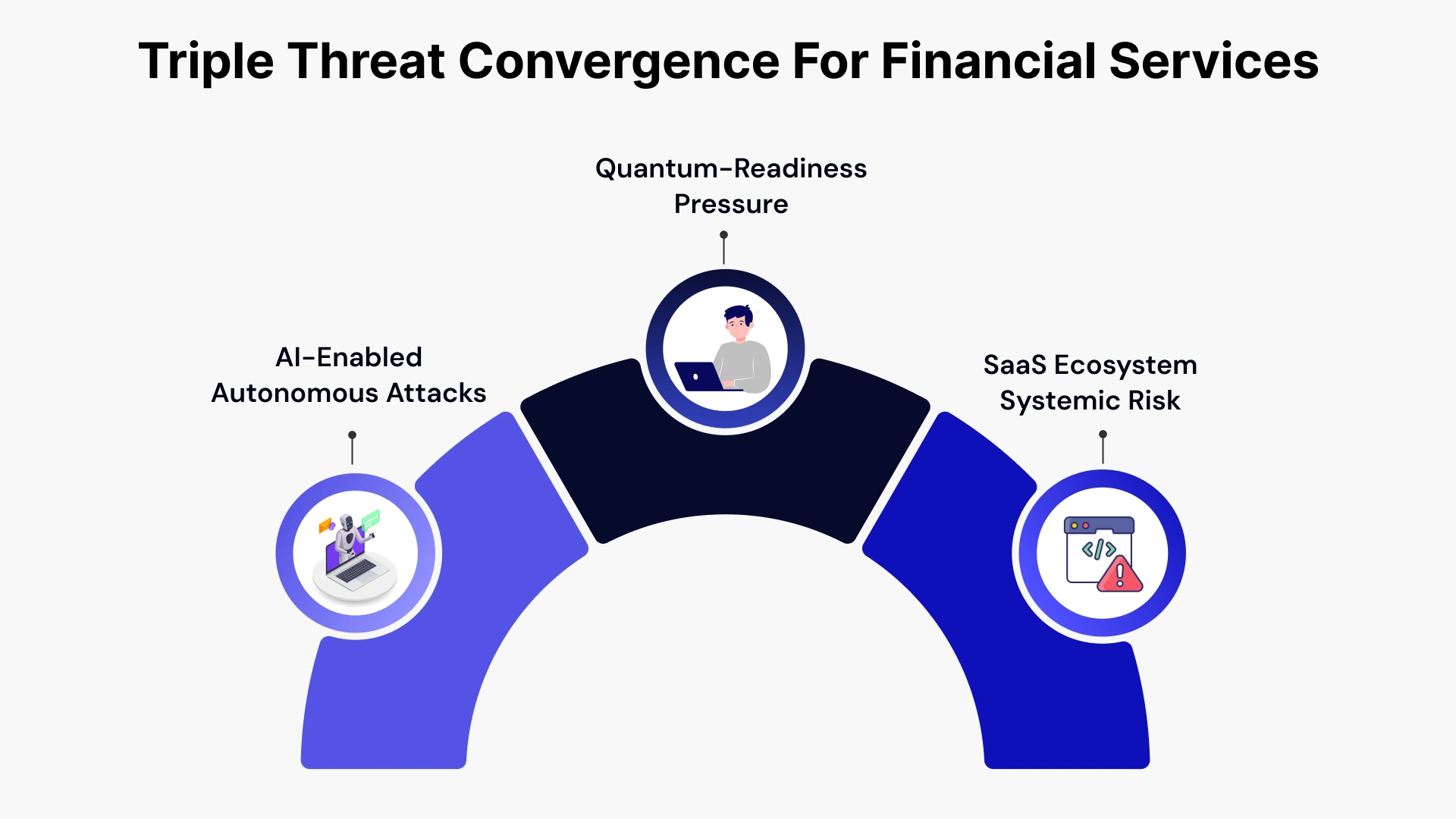
What Are the Key Cybersecurity Trends in Financial Services in 2026?
The financial services cybersecurity trends in 2026 reflect a sector under sustained, intelligent, and increasingly autonomous attack — while simultaneously navigating the most complex regulatory environment in its history. Seven trends demand immediate attention from every North American CISO and CTO.
Key cybersecurity trends in financial services in 2026:
Here are the key financial services cybersecurity trends shaping the industry this year:-
Pro Tips: Businesses evaluating Key cybersecurity trends in financial services in 2026: should also consider cybersecurity solutions for Connecticut financial firms to improve execution quality, scalability, and long-term operational resilience.
1. AI as Both Attacker and Defender — The Double-Edged Reality
In 2026, AI is the most consequential force reshaping the financial services threat landscape — on both sides.
On the offense side, threat actors are weaponizing generative AI to produce real-time deepfake video and voice for KYC bypass, generate synthetic identities that pass credit decisioning models, craft hyper-personalized spear-phishing targeting C-suite executives, and automate vulnerability discovery and lateral movement across cloud environments.
On the defense side, institutions like JPMorgan Chase have scaled AI-driven security operations to analyze billions of log events daily — identifying 'slow-and-low' data exfiltration patterns invisible to human analysts. AI-powered behavioral analytics now detect anomalous transaction patterns, insider threat signals, and API abuse in near-real-time.
The critical risk governance question for 2026: As institutions deploy internal AI and large language models (LLMs) for finance software solutions and compliance workflows, these models themselves become high-value attack surfaces. Prompt injection attacks — where adversaries manipulate AI model inputs to exfiltrate data or bypass controls — are emerging as a priority threat category (FS-ISAC 2026).
What this means for your 2026 roadmap:
- Deploy AI-native detection alongside rule-based SIEM/SOAR
- Establish AI model governance policies before deploying internal LLMs
- Implement 'Liveness 2.0' multi-modal biometrics for KYC (photoplethysmography + challenge-response)
2. Identity-First Security and Zero Trust as the New Standard
The enterprise perimeter is gone. In a cloud-first, open-banking API environment, the identity of the user, the device, and increasingly the AI agent is the only valid security boundary. Zero Trust Architecture (ZTA) — never trust, always verify — is now table stakes for North American FSIs.
However, adoption depth is uneven. 78% of banks have 'integrated ZTA principles,' but fewer have achieved continuous adaptive authentication across hybrid environments. In 2026, two specific gaps are being exploited: MFA fatigue attacks (overwhelming users with push notifications until they accidentally approve) and session hijacking post-authentication. Standard SMS and push-based MFA are no longer sufficient.
API-first banking under Section 1033 open banking requirements creates an additional identity challenge: machine-to-machine API authentication now requires the same rigor as human authentication.
3. Cloud Security and Third-Party Concentration Risk
The financial sector's migration to the cloud has created a paradox: efficiency gains are accompanied by dangerous concentration risk. When a single hyperscaler or core SaaS platform experiences an outage or breach, the blast radius now extends across dozens of interconnected institutions.
Goldman Sachs' implementation of mandatory Software Bills of Materials (SBOMs) for every third-party vendor — allowing identification of vulnerable libraries across their entire stack within minutes — represents the operational standard other institutions must now reach. Capital One's use of advanced encryption with bank-held keys ensures that even a cloud provider compromise leaves financial data unreadable.
Cloud-Native Application Protection Platforms (CNAPP) are consolidating visibility across virtual machines, containers, and serverless functions — replacing the fragmented point-solution approach that creates detection gaps.
For CISOs, 2026 cloud security priorities include:
- SBOM requirements for all third-party and SaaS vendors
- CNAPP deployment for unified cloud workload visibility
- Contractual resilience clauses covering RTO/RPO obligations for critical SaaS
- Multi-cloud failover architecture for mission-critical workloads
4. Post-Quantum Cryptography — The 2030 Countdown
Quantum computing represents a slow-moving but existential threat to current encryption standards. The 'Harvest Now, Decrypt Later' (HNDL) attack model means adversaries are already collecting encrypted financial data — customer records, transaction histories, regulatory filings — with the intent to decrypt once quantum capability reaches the RSA/ECC breakage threshold.
NIST standardized its first post-quantum algorithms in 2024 (including ML-KEM). The Q-Day risk deadline is estimated between 2029-2032. CISOs in North American financial services need a structured migration path today.
| Stage | Action | Timeline |
| 1. Discovery | Inventory all asymmetric encryption (PKI, TLS, SSH) across enterprise | Q1-Q2 2026 |
| 2. Prioritization | Categorize data by 'shelf life' — trust docs, regulatory records = highest priority | Q2 2026 |
| 3. Crypto-Agility Testing | Implement frameworks allowing algorithm swaps without app re-architecture | Q3 2026 |
| 4. PQC Integration | Deploy NIST ML-KEM in hybrid mode alongside classical encryption | Q4 2026 onward |
5. Autonomous SOC and AI-Powered Defense
Tier 1 and Tier 2 SOC analyst functions are now 90% automated in leading financial institutions. AI-driven detection handles alert triage, initial investigation, and playbook execution. Human threat hunters intervene only for architectural anomalies, novel attack chains, and high-judgment escalations.
This shift has a direct talent implication: the CISO's hiring strategy is evolving from 'analysts who write SIEM queries' to 'engineers who tune detection models and manage AI security platforms.' Institutions that don't adapt their operating model will face both security gaps and talent market disadvantages.
6. Ransomware and Supply Chain Attacks Targeting Core Banking
Ransomware attacks on financial services have shifted from opportunistic encryption to targeted operational disruption — threatening payment rails, clearing functions, and trading platforms. FS-ISAC 2026 data highlights the rise of attacks on core banking systems wrapped in cloud APIs, exploiting the visibility gap between legacy systems and their cloud-native interfaces.
Supply chain attacks now target the software development pipelines of core banking vendors themselves — inserting malicious code upstream that propagates to hundreds of dependent institutions. A 2026-era 'Log4j-equivalent' event in a widely-used fintech middleware layer would have devastating sector-wide consequences.
7. Regulatory-Driven Transparency and Disclosure Obligations
Regulators are no longer accepting annual compliance attestations as evidence of security. The new standard is continuous, auditable evidence of control effectiveness. In the US, the SEC's cyber disclosure rules require material incident reporting within 4 business days.
NYDFS 500 amendments demand annual certification from CISOs on the effectiveness of covered entity security programs. This regulatory pressure is transforming cybersecurity from an operational concern into a governance and disclosure obligation.
Regulatory and Compliance Landscape Shaping Financial Cybersecurity
What regulations affect cybersecurity in financial services? In North America, financial institutions face the most demanding and fragmented regulatory environment in history — and for institutions with cross-border operations, the complexity multiplies further.
United States Regulatory Drivers
- SEC Cyber Disclosure Rules (Effective December 2023, enforcement ramping in 2026): Public financial companies must disclose material cybersecurity incidents within 4 business days and provide annual disclosures on cybersecurity risk management, strategy, and governance. This has elevated the CISO to a board-reporting function.
- NYDFS Cybersecurity Regulation (Part 500 — Amended 2023): Expanded requirements for covered entities include CISO certification of security programs, penetration testing, vulnerability management, and MFA across all systems. The 2024 enforcement actions against financial firms set a high-water mark for penalty expectations.
- FINRA Cybersecurity Guidance: Broker-dealers face heightened expectations on incident response, vendor management, and business continuity — with examination focus areas including managed cloud services , security controls, and third-party risk assessment.
- Open Banking / Section 1033 (CFPB Final Rule): Effective from 2026, requires financial data providers to support consumer-authorized data sharing — dramatically expanding API attack surface and creating new identity and access management obligations.
Canada and Cross-Border Complexity
- OSFI Guideline B-13 (Technology and Cyber Risk): Canada's primary bank regulator expects detailed technology and cyber risk management programs, including third-party risk frameworks, incident notification, and resilience testing. Failure to align with B-13 creates examination risk for Canadian operations of US banks.
- Bill C-26 (Critical Cyber Systems Protection Act): Once enacted, will impose mandatory incident reporting and cybersecurity program requirements on federally regulated financial institutions in Canada — creating a DORA-equivalent framework for cross-border institutions.
- DORA (EU Digital Operational Resilience Act — Applicable from January 2025): US financial institutions with EU operations or significant EU counterparty relationships face DORA's operational resilience testing, ICT third-party risk management, and incident classification requirements. Cross-border compliance alignment is now a mandatory CISO program element.
| Regulation | Jurisdiction | Key 2026 Obligation | CISO Action Required |
| SEC Cyber Disclosure | US (Public Companies) | 4-day material incident disclosure | Incident classification framework, board reporting cadence |
| NYDFS Part 500 | New York State | CISO annual certification | Program documentation, penetration testing cadence |
| OSFI B-13 | Canada | Tech and cyber risk management | Third-party risk program, resilience testing |
| DORA | EU (cross-border impact) | Operational resilience testing, ICT risk | ICT third-party register, TLPT testing |
| Section 1033 / CFPB | US | API data sharing security | API security controls, consumer consent management |
Cybersecurity Budgets, Operating Models, and Talent in 2026
How are financial institutions structuring their security investments in 2026? The data points to a decisive shift: cybersecurity has become the top driver of IT budget growth in financial services, not an allocated overhead line.
Security as a Line Item in Institutional Valuation
The connection between cyber posture and institutional valuation is now direct. Cyber insurers are demanding real-time EDR and XDR telemetry before renewing policies — static annual questionnaires are no longer accepted. Investors and rating agencies increasingly factor cyber maturity into credit assessments. For publicly traded FSIs, a material breach under the SEC disclosure regime can trigger an immediate market valuation impact.
2026 budget allocation is shifting toward: AI-driven detection and response platforms, identity and access management (IAM) modernization, cloud security posture management (CSPM/CNAPP), compliance automation and GRC platforms, and post-quantum cryptography migration programs.
The Rise of Managed and Co-Managed Security Models
The talent shortage in cybersecurity — with an estimated 3.4 million unfilled positions globally — is driving financial institutions toward managed cybersecurity services, SOC-as-a-Service, and co-managed security operating models. This shift is not driven by cost alone.
The complexity of the 2026 threat environment — AI-driven attacks, multi-cloud environments, cross-jurisdiction compliance — exceeds the capacity of even well-resourced in-house teams.
| Capability | In-House | Co-Managed | Fully Managed |
| 24/7 Threat Monitoring | High cost, talent risk | Shared responsibility, faster scale | Provider-led, SLA-driven |
| Compliance Automation | Custom build required | Shared platform, joint tuning | Vendor-managed, audit-ready |
| Incident Response | Internal team, variable capacity | Augmented by provider playbooks | Provider-led with FS specialization |
| Cloud Security Posture | Requires specialist hire | Co-managed CNAPP deployment | Fully managed CSPM service |
| Threat Intelligence | Open-source + subscription | Enhanced with provider TI feeds | Curated FS-sector intelligence |
The optimal model varies by institution size and risk profile — but the direction of travel is clear. Even Tier 1 institutions are moving toward co-managed SOC models to address the AI threat velocity gap.
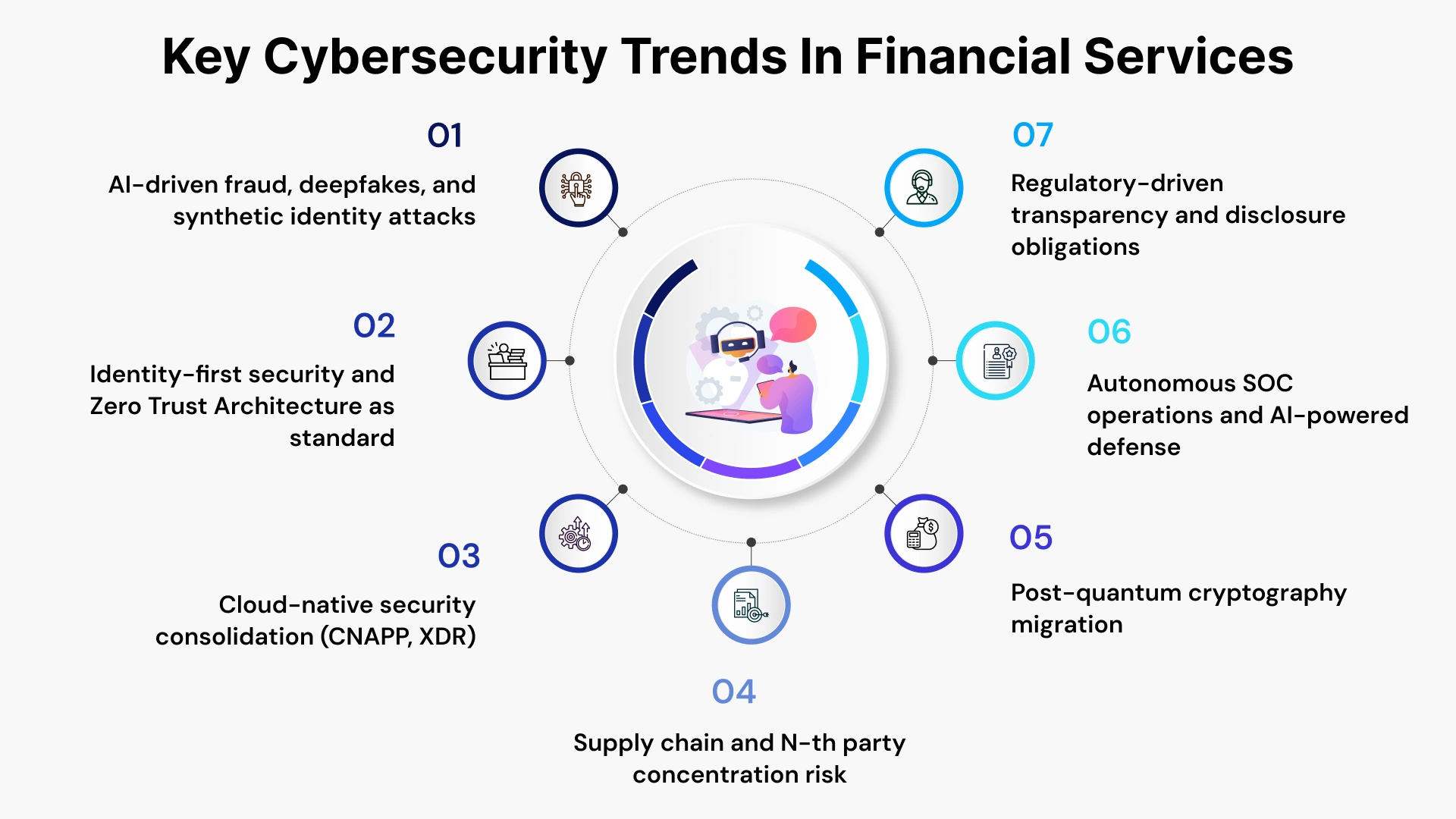
Building Operational Resilience in Financial Services
How can financial institutions improve cyber resilience in 2026? Regulators, insurers, and counterparties are no longer satisfied with incident response plans that exist only in documents. They require demonstrated, tested resilience.
From Incident Response to Continuous Resilience
The 2026 resilience standard requires continuous testing, not annual exercises. Key components:
1. Identity hardening: Implement phishing-resistant MFA (FIDO2/passkeys), privileged access workstations, and just-in-time access provisioning for all administrative functions.
2. Continuous monitoring: Deploy 24/7 AI-augmented SOC with behavioral baselines for all critical financial workflows — payments, clearing, credit decisioning.
3. Third-party stress testing: Conduct quarterly tabletop exercises that simulate SaaS provider failure, supply chain compromise, and core banking system unavailability. Recovery Time Objectives (RTOs) must be defined and tested — not assumed.
4. Compliance automation: Implement Compliance-as-Code (CaC) frameworks that continuously map technical controls to SEC, NYDFS, OSFI, and DORA requirements — eliminating the audit preparation sprint.
5. AI-based anomaly detection: Establish behavioral baselines for all users, service accounts, and AI agents — flagging deviations that precede exfiltration or lateral movement.
Cloud and Third-Party Outage Preparedness
The concentration risk of cloud dependency requires an explicit multi-cloud failover architecture for mission-critical workloads. Key elements for North American institutions:
- Contractual resilience clauses: Vendor SLAs must specify RTO/RPO obligations, incident notification timelines, and audit rights — not just uptime percentages.
- SBOM audits: Maintain a current inventory of all software components in third-party and SaaS solutions. When a new vulnerability is discovered, the time to identify affected systems drops from weeks to hours.
- Geographic failover: For institutions subject to DORA or OSFI B-13, multi-region failover is now an examination expectation, not merely a best practice.
- Tabletop scenarios: Simulate a major cloud provider outage coinciding with a ransomware event — the dual-crisis scenario that stress-tests both technical and governance response simultaneously.
A 2026 Roadmap for CISOs and CTOs: From Trends to Decisions
A financial services cybersecurity trend report is only as valuable as the actions it inspires. Moving beyond mere observation, the following 2026 roadmap provides a prioritized execution strategy organized by investment horizon.
Quick Wins (0-6 Months)
- Credential hardening: Audit all accounts for weak passwords, shared credentials, and inactive accounts. Deploy phishing-resistant MFA across all privileged and external-facing systems.
- Third-party inventory: Produce a complete register of all SaaS, cloud, and third-party software dependencies. Initiate SBOM requests from critical vendors.
- SEC/NYDFS compliance readiness: Validate your material incident classification framework and 4-day disclosure workflow. Simulate a regulatory notification exercise.
- AI governance foundation: Document all internal AI and LLM deployments. Establish model risk management policies before next-generation AI tools enter production.
Strategic Bets (12-36 Months)
- Post-quantum migration program: Complete cryptographic inventory and begin hybrid PQC deployment for highest-priority data categories (trust documents, long-life customer records).
- AI SOC automation: Evaluate co-managed SOC options or invest in AI-native SIEM/SOAR platforms that reduce analyst alert fatigue and accelerate mean-time-to-respond (MTTR).
- Compliance-as-Code: Build automated control mapping across all applicable regulatory frameworks — eliminating the manual evidence-gathering cycle that consumes CISO team capacity.
- Zero Trust maturity progression: Move from perimeter-ZTA toward continuous adaptive authentication covering all users, devices, APIs, and AI agents.
| Initiative | Risk Impact | Regulatory Pressure | ROI Horizon | Priority |
| Phishing-Resistant MFA | High | High (NYDFS, OSFI) | 0-6 months | Immediate |
| Third-Party SBOM Program | High | Medium | 0-6 months | Immediate |
| AI-Driven Detection (SOC) | High | Medium | 6-12 months | High |
| PQC Migration - Phase 1 | Medium-High | Medium (NIST pressure) | 12-24 months | High |
| Compliance-as-Code Platform | Medium | High (multi-regime) | 12-18 months | High |
| CNAPP/Cloud Security | High | Medium-High | 6-12 months | High |
| Operational Resilience Testing | High | High (DORA, OSFI) | Ongoing | Ongoing |
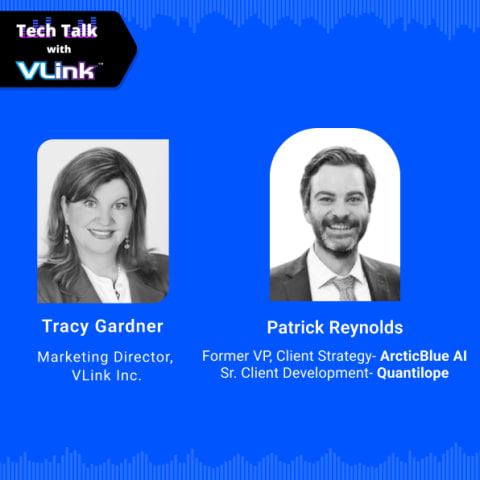
Leveraging VLink Expertise for Managed Cybersecurity Services
The 2026 cybersecurity landscape demands both breadth and depth that exceed the internal capacity of most financial institutions. The financial services cybersecurity trends outlined in this report — AI-enabled threats, multi-regime regulatory compliance, post-quantum cloud migration consulting services, cloud concentration risk — require specialized expertise, 24/7 operational coverage, and technology platforms that few institutions can build entirely in-house.
VLink's Microsoft business solutions are purpose-built for North American financial services institutions navigating exactly this environment. Our capabilities span:
- Managed Detection and Response (MDR): AI-augmented 24/7 SOC operations with financial services-specific threat intelligence, behavioral analytics, and accelerated MTTR.
- Cloud Security Services: CNAPP deployment, cloud security posture management, and third-party risk programs designed for multi-cloud financial environments — covering AWS, Azure, and GCP workloads with FS-regulatory alignment.
- Compliance Automation and GRC: Compliance-as-Code frameworks that continuously map controls to SEC, NYDFS Part 500, OSFI B-13, and DORA — reducing audit preparation cycles from months to days.
- Identity and Zero Trust Programs: IAM modernization, phishing-resistant MFA deployment, privileged access management, and zero trust architecture design for hybrid banking environments.
- Incident Response and Resilience: Retainer-based IR services, tabletop exercise facilitation, and regulatory disclosure support under SEC 4-day reporting requirements.
Our dedicated team brings direct experience with Tier 1 and regional bank security programs — translating the trends in this report into executable, board-ready roadmaps and operating model decisions.
Conclusion
The financial services sector in 2026 is navigating a period of profound cyber risk evolution. AI-powered attacks are autonomous and industrialized. Regulators are demanding real-time accountability. The SaaS ecosystem has created systemic concentration risk that individual institutions cannot fully control.
The CISOs and CTOs who will lead their institutions through this environment are those who shift from reactive defense to proactive resilience — treating cyber risk as a board-level business metric, embedding compliance into continuous operations, and building the partnerships necessary to close the velocity gap between attacker innovation and institutional response.
The threat environment will not simplify. But with the right frameworks, operating model, and strategic investments, North American financial institutions can turn their cyber programs from a source of institutional risk into a source of competitive trust.
Don't navigate this evolving threat landscape alone. VLink combines deep technical expertise with regulatory foresight to help financial institutions build resilient, AI-ready security infrastructures that withstand modern threats. Contact us today for a strategic assessment.

Account Executive, VLink Inc.
Sandeep Panchal is an experienced Account Executive with a strong background in the information technology and services sector. He has a solid track record in account P&L management, sales strategy execution, CRM, market research, technical recruiting, and IT staffing services.








 Shivisha Patel
Shivisha Patel