David Okafor, CTO of a Schedule I Canadian bank headquartered in Toronto, began 2026 with a clear operational mandate but a constrained execution window. OSFI's Guideline E-21, requiring full adherence by September 1, 2026, placed the bank's core banking resilience framework under direct supervisory scrutiny.
Meanwhile, the bank's trading infrastructure still ran on COBOL-era middleware. Three separate data stores held conflicting client records across retail, institutional, and wealth divisions. And a FinTech competitor had just launched a fully cloud-native payments product that onboarded institutional clients in under 48 hours — compared to the bank's 14-day manual process.
Okafor was not dealing with a technology backlog. He was managing a structural capability gap — one that affected regulatory standing, competitive positioning, and the bank's ability to deploy AI at scale.
This scenario is not hypothetical.
Legacy application modernization is no longer a back-office IT project. For Canada's Big 6 banks and their mid-tier counterparts, it is the foundational decision that determines whether they can meet OSFI deadlines, deploy AI on meaningful workloads, and compete with digital-first challengers on product velocity.
This blog maps the strategic landscape — what is driving the urgency, what the proven modernization approaches look like in practice, and where the hidden execution risks live.
The Canadian Legacy Banking Dilemma: A Data-Led Picture
In Canada specifically, the pressure compounds. OSFI's data collection modernisation initiative — officially launched in January 2026 — represents the most significant regulatory technology upgrade in Canadian banking history. The Bank of Canada, OSFI, and CDIC have spent three years building a new regulatory reporting framework, with the planning phase completing in April 2025 and implementation now underway (FundMore.ai, January 2026). Banks that cannot align their data architecture to this new framework face supervisory and reporting exposure.
Why 2026 Is the Year Legacy Debt Becomes a Board-Level Priority
Three forces converge in 2026 to make legacy modernisation a board-level conversation — not a technology committee discussion.
OSFI compliance deadlines are live and non-negotiable.
Full adherence to Guideline E-21 is required by September 1, 2026. The guideline mandates that federally regulated financial institutions (FRFIs) identify critical operations, set disruption tolerances, map technology dependencies end-to-end, and complete scenario testing. For most Canadian banks, meeting E-21's dependency-mapping requirement directly surfaces the brittleness of their legacy infrastructure — making modernisation a compliance prerequisite, not just an innovation initiative.
Cyber risk exposure from legacy systems is measurable and worsening.
Priority 1 cyber incidents against Canadian financial institutions have nearly tripled since 2022 (Global Relay, 2026). Legacy systems — particularly COBOL-based cores with no native API layer, minimal encryption at rest, and batch-processing architectures — create an expanded attack surface that modern Zero Trust security models cannot adequately protect without architectural remediation.
The AI opportunity window is closing for firms without a modernised data infrastructure.
PwC Canada's 2025 banking outlook noted that generative and agentic AI remain largely in exploratory stages for most Canadian banks — but the institutions deploying AI development services in production share one common characteristic: they have already modernised their data layer. CIBC's AI deployment, which scaled from 500 to over 7,500 employees after a successful pilot and saved more than 200,000 hours of work, was built on a modernised Azure infrastructure — not on legacy middleware. (Microsoft, January 2026).
OSFI E-21 and B-13: The Regulatory Deadlines Forcing the Conversation
Understanding the OSFI regulatory framework is essential context for any legacy modernisation decision in Canada. Two guidelines operate in direct alignment with technology infrastructure decisions.
- OSFI Guideline E-21 (Operational Risk Management and Resilience) establishes four phased requirements: governance frameworks effective August 2024; operational risk management full adherence due September 2025; complete guideline adherence due September 1, 2026; and scenario testing covering all critical operations due September 1, 2027. The guideline explicitly connects to technology infrastructure: institutions must map every dependency supporting a critical operation, including underlying systems, third-party services, data stores, and integration middleware. A legacy monolith with undocumented integration points fails this test.
- OSFI Guideline B-13 (Technology and Cyber Risk Management) aligns with E-21 to address the technology-specific dimensions of operational resilience. B-13 places emphasis on data integrity and lineage, technology risk governance, vendor and third-party oversight, and the ability to detect, respond to, and recover from technology failures. Banks still running COBOL cores through proprietary middleware with no API documentation face a direct B-13 compliance gap — one that requires architectural remediation, not just policy updates.
The September 2026 deadline is not aspirational. OSFI has committed to selective supervisory reviews during the phased implementation period. Institutions that cannot demonstrate E-21 and B-13 adherence through evidence — dependency maps, scenario test results, and technology risk assessments — face regulatory exposure that extends beyond a paper finding.
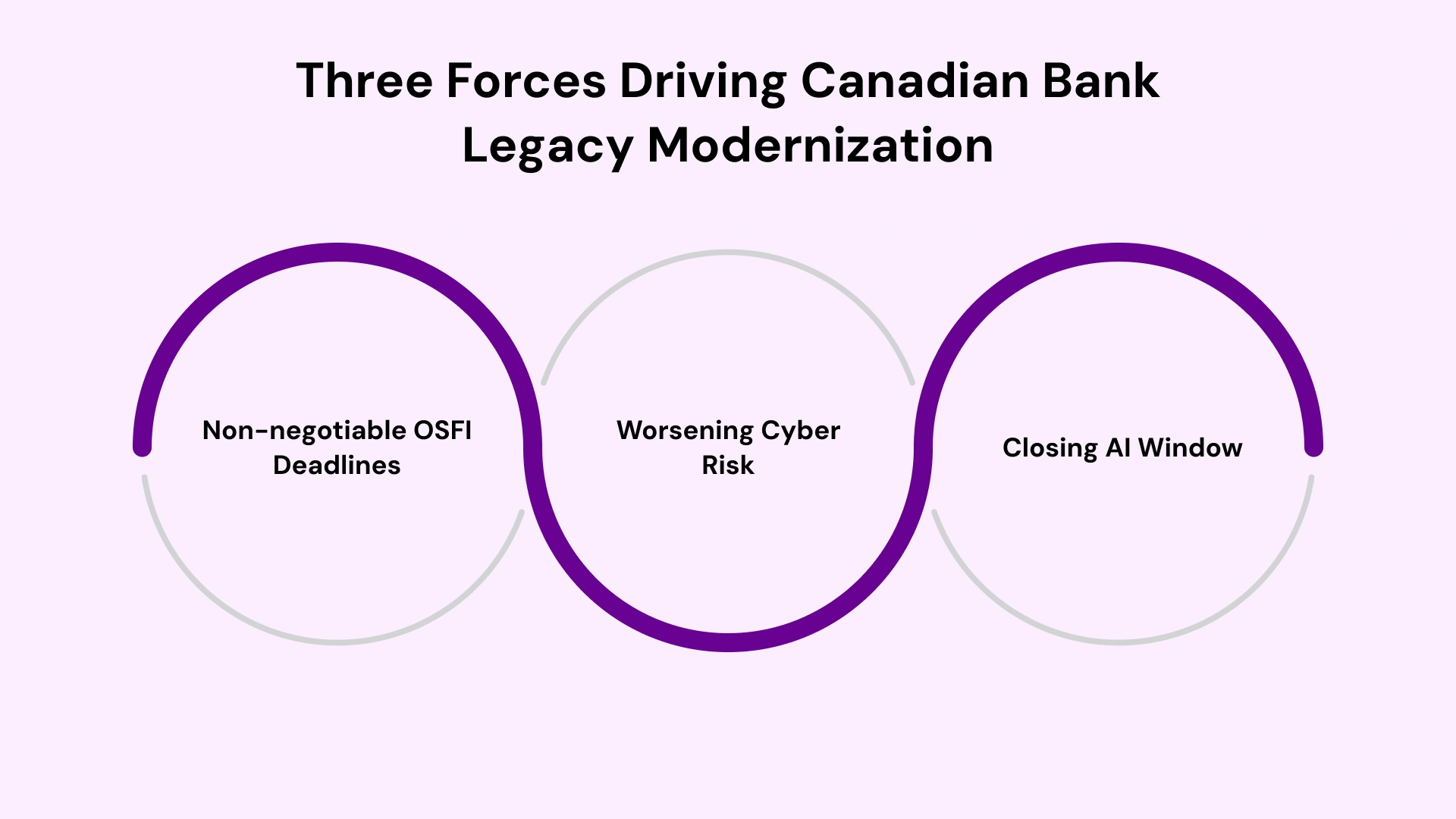
The 6 Rs Framework: Choosing the Right Modernization Strategy
Not all legacy systems warrant the same modernisation treatment. The 6 Rs framework — Rehost, Replatform, Refactor, Re-architect, Replace, and Retire — gives CTOs and Heads of Digital Transformation a structured methodology for classifying each system before committing budget.
- Table: 6 Rs Legacy Modernization Framework for Canadian Banks
Strategy | Definition | Best Fit | Risk Level |
Rehost | Lift-and-shift to cloud without code changes | Non-critical batch systems needing rapid cloud migration | Low |
Replatform | Move to the cloud with minor optimisations | Mid-tier reporting and data systems | Low-Medium |
Refactor | Rewrite code without changing architecture | Performance-critical modules with stable business logic | Medium |
Re-architect | Decompose monolith into microservices | Core banking systems blocking fintech integrations | Medium-High |
Replace | Swap legacy system for a commercial platform | Point solutions with available SaaS alternatives | High |
Retire | Decommission redundant systems | Duplicate or shadow systems with no active users | Low |
For Canadian banks, the practical modernisation sequence typically combines Rehost for non-critical batch workloads, Re-architect for the core banking monolith using the strangler fig pattern, and Replace for point solutions where mature SaaS alternatives exist. The sequencing matters: attempting to re-architect the core before stabilising the data architecture consistently produces longer timelines and higher risk.
From COBOL to Cloud-Native: Core Banking Modernization Approaches
The core question for most Canadian bank CTOs is not whether to modernise COBOL — it is how to sequence that transition without disrupting the systems that process millions of transactions daily. COBOL talent scarcity is a material constraint: qualified COBOL and mainframe engineers command over $150,000 annually in the North American market, and the developer pool contracts further each year as practitioners retire without successors (SoftwareModernizationServices.com, 2026).
AI-assisted modernisation tools are changing this calculus: the average cost of a COBOL modernisation project dropped from $9.1 million in 2024 to $7.2 million in 2025 as AI-powered automation took over dependency mapping, code analysis, and test suite generation (GUVI, 2026).
The Strangler Fig Pattern is the dominant architecture approach for large-scale core banking modernisation in Canada. Rather than a rip-and-replace rewrite — which introduces unacceptable downtime risk for mission-critical transaction systems — the strangler fig pattern builds new microservices around the legacy monolith's edges. An API gateway intercepts inbound requests, routing specific functions to new services while the remaining traffic continues through the legacy core. Royal Bank of Canada (RBC) publicly acknowledged the need to 'renew legacy infrastructure to ensure ongoing resiliency' as part of its strategy (mobileLIVE, 2025), reflecting the industry-wide recognition that incremental de-risking beats big-bang replacement.
Canada's own EQ Bank offers a reference point for the destination state: EQ Bank became Canada's first cloud-native bank in 2019, demonstrating that full cloud-native architecture is achievable for Canadian institutions operating under OSFI's regulatory framework. The Legacy System Modernization Services approach that consistently produces results combines strangler fig decomposition with parallel-run architecture — running new and legacy systems in synchrony, validating output equivalence before any cutover, and retiring legacy modules only after the new service has earned production trust.
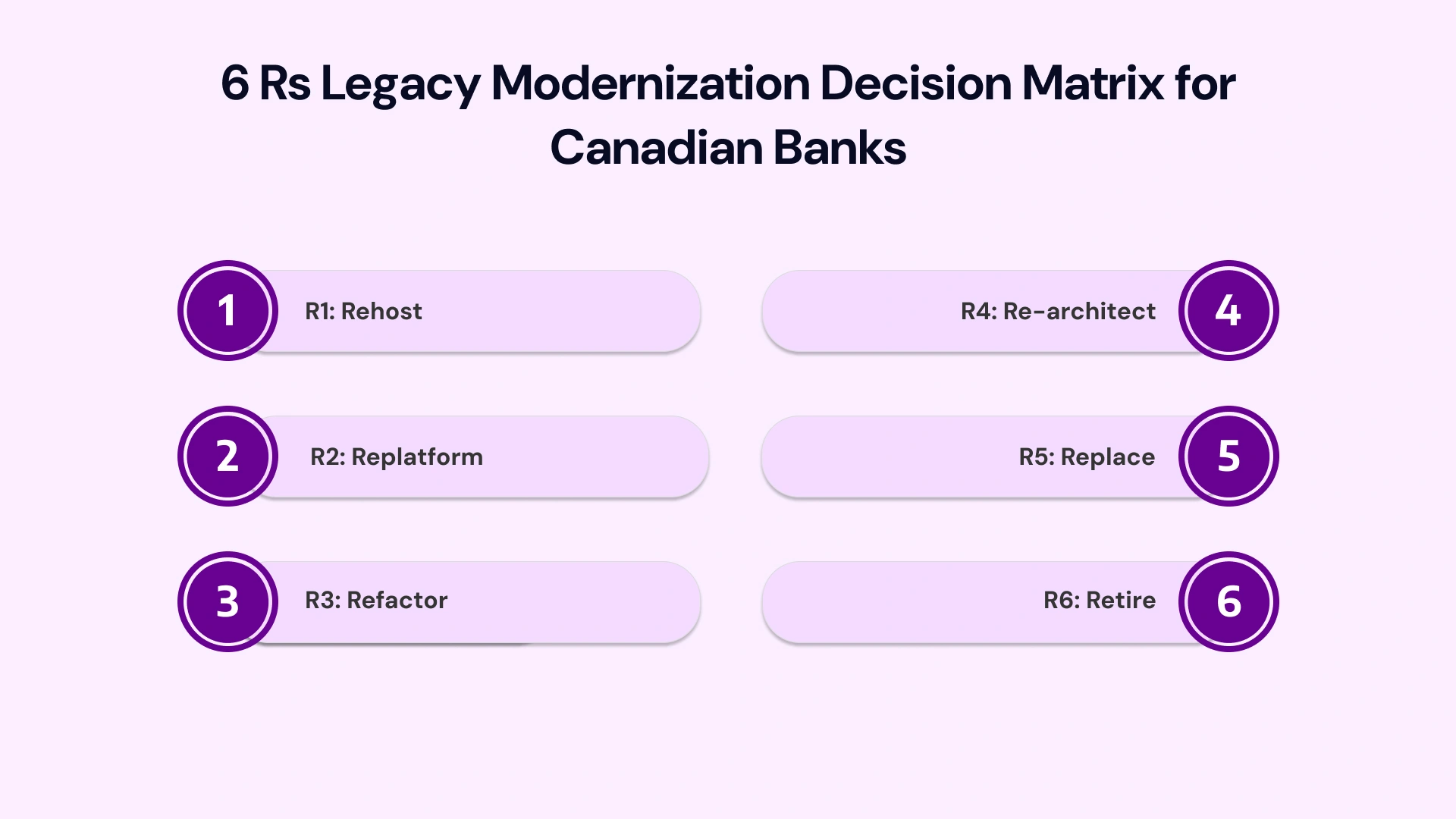
Middleware, MQ, and Integration: The Missing Layer Most Programmes Ignore
Most legacy modernisation programmes focus on the application layer — the COBOL core, the monolithic reporting system, the aging data warehouse. What they consistently underestimate is the integration layer: the middleware, message queues, and enterprise service buses that connect applications across the bank's technology estate. This is where the most expensive and dangerous gaps appear.
WebSphere MQ (IBM MQ) remains the dominant messaging backbone at most Canadian Tier 1 and Tier 2 banks. It handles high-volume, high-reliability message queuing across trading systems, payment rails, core banking, and back-office reconciliation. When a bank modernises its core banking layer without accounting for MQ-dependent downstream systems — clearing, settlement, compliance reporting, SWIFT integrations — the result is broken message contracts, data loss, and failed transactions that surface only in production.
IBM Integration Bus (IIB) / App Connect Enterprise and WebSphere Transformation Extender (WTX) present a related challenge. Many Canadian banks run complex data transformation logic embedded in WTX maps — translating between legacy formats, SWIFT MT standards, ISO 20022, and proprietary data schemas. Modernising the applications that produce and consume those transformations without re-engineering the WTX maps creates a brittle integration layer that fails under load or during format changes.
The correct approach treats middleware modernisation as a parallel workstream alongside core banking migration — not a post-migration cleanup task. This means inventorying every MQ queue, IIB integration flow, and WTX transformation map before any application cutover; establishing API-based message contracts that allow new services and legacy middleware to coexist during the transition; and planning the eventual migration from proprietary middleware to event-driven architecture as a distinct, phased programme.
Banks that invest in this integration layer upfront — building a governed middleware inventory and transformation map before cutting over any core system — consistently reduce their legacy modernization in capital markets programme risk by 30 to 40 percent compared to application-first programmes that discover integration gaps in late-stage testing.
API-First and Microservices: Building the Architecture Layer for Tomorrow
An API-first architecture is not simply a technology decision — it is a product capability decision. Banks that expose core banking functions (account data, payment execution, KYC status, credit decisions) as governed, versioned APIs gain two compounding advantages: they can integrate with fintech partners without exposing legacy system internals, and they can replace underlying systems incrementally without breaking the API contracts that downstream teams depend on.
For Canadian banks pursuing Cloud Consulting Services and hybrid cloud infrastructure strategies, the API gateway layer serves as the control plane for workload routing. New microservices deployed on cloud-native infrastructure register with the gateway; legacy COBOL services route their traffic through the same gateway under governed contracts. This architecture enables the strangler fig pattern at scale — new services gradually absorb traffic from legacy counterparts until the legacy module can be safely retired.
The microservices banking architecture that emerges from this pattern is not a monolith replacement — it is a portfolio of independently deployable services with explicit contracts, circuit breaker patterns, and observability stacks. Each service has its own SLO, its own deployment cadence, and its own fault isolation boundary. A failure in the account notification service does not cascade to the payment processing service — the blast radius of any failure is contained by design.
The practical implementation timeline for an API-first microservices transition at a Canadian Schedule I bank typically spans 18 to 36 months, depending on the complexity of the legacy estate and the number of downstream integration consumers. Firms attempting to compress this timeline without adequate integration inventorying consistently encounter the same failure: a new microservice that breaks three legacy downstream consumers at cutover because the message contract was not fully mapped.
Legacy vs. Modernized Systems: A Decision-Maker's Comparison
Senior IT leaders evaluating the modernisation business case need a clear side-by-side view of what the current state costs against what the modernised state delivers. The table below maps the dimensions that matter most to COOs, CTOs, and Heads of Digital Transformation in Canadian banking.
- Table: Legacy vs. Modernized Core Banking Systems — Canadian Banking Context
Dimension | Legacy System State | Modernized System State |
OSFI E-21 Compliance | Dependency mapping incomplete; resilience testing fails | Full dependency map; scenario testing embedded in operations |
COBOL Talent Risk | Shrinking developer pool; $150K+ per specialist | AI-assisted code conversion; no COBOL dependency |
Time to Deploy New Features | 6–18 months for core changes | 2–6 weeks via independent microservice deployment |
Fintech Integration | Point-to-point, bespoke integration per partner | API gateway; self-service onboarding in days |
Data Lineage for OSFI Reporting | Manual extraction; inconsistent golden source | Real-time data fabric; automated audit trail |
AI/ML Readiness | Siloed data; no feature store; model deployment blocked | Cloud-native data lakehouse; MLOps pipeline ready |
IT Maintenance Cost | 60–80% of IT budget on legacy upkeep | Reduced to 20–30% post-modernisation |
Cyber Risk Posture | Expanded attack surface; batch processing gaps | API-level security; Zero Trust architecture |
Building the Business Case: From IT Priority to Board Mandate
The most common execution barrier for Canadian bank CTOs is not the modernisation strategy — it is the business case. Legacy application modernisation competes for capital against revenue-generating initiatives. Framing it as a technology upgrade loses the board vote. Framing it as a risk mitigation, regulatory compliance, and competitive capability decision wins it.
The Risk Frame: Quantify the Cost of Inaction
Legacy maintenance consumes 60 to 80 percent of most Canadian bank IT budgets, leaving 20 to 40 percent for innovation. Every year of delay compounds the tech debt paydown required later. OSFI E-21 supervisory reviews create direct regulatory exposure if dependency mapping reveals undocumented legacy connections. Cyber incident costs from legacy-related breaches — incident response, regulatory fines, and reputational impact — routinely exceed modernisation programme costs for a Tier 1 institution.
The Opportunity Frame: Quantify the Enabling Capability
A modernised core banking platform reduces product time-to-market from months to weeks. API-first architecture enables fintech partnerships that generate new revenue streams without building from scratch. AI readiness — specifically, a clean data layer with governed lineage — is the prerequisite for deploying the AI and automation tools that PwC Canada and CSI's 2026 Banking Priorities survey both identify as the primary value driver for Canadian banks over the next three years. The 2026 Banking Priorities Executive Report found AI named the most significant technology trend for the third consecutive year, up 19 percentage points from 2025.
The business case that wins at the board level combines both frames: quantified regulatory risk from E-21 non-compliance, quantified tech debt paydown cost over five years, and quantified revenue upside from two to three specific products that become feasible only after modernisation — expressed in NPV terms over a 36-month horizon.
How VLink Supports Canadian Banks Through Legacy System Modernization
VLink's delivery teams bring direct execution experience across the specific systems that define the Canadian banking legacy challenge. Our practice covers WebSphere MQ, WTX (WebSphere Transformation Extender), IIB (IBM Integration Bus), and enterprise middleware integration — the integration layer that most modernisation programmes underestimate and most programmes fail on.
Our dedicated team delivers Legacy System Modernization Services for financial institutions using a structured, zero-downtime methodology: complete integration of inventory before any code change, parallel-run architecture during transition, output equivalence validation before cutover, and phased legacy retirement after production validation. Our teams have executed modernisation programmes for banking and insurance clients across North America, including institutions operating under OSFI E-21 and B-13 compliance frameworks.
Our service coverage for Canadian banking modernisation includes: core banking application modernisation using the strangler fig pattern; COBOL and mainframe migration with AI-assisted code analysis; WebSphere MQ and IIB integration layer assessment and re-architecture; hybrid cloud migration with OSFI data residency compliance; and API-first microservices architecture design and implementation.
Engagements begin with a Legacy System Assessment — a four-to-six-week diagnostic that maps your full technology estate, identifies OSFI E-21 dependency gaps, quantifies your tech debt exposure, and produces a sequenced modernisation roadmap with business-case-ready ROI projections. This assessment is the starting point for every programme — because institutions that begin execution without architectural clarity consistently discover the most expensive surprises in late-stage testing.
Conclusion: Legacy Modernization Is a 2026 Execution Decision
The Canadian banking sector enters 2026 with three forces aligned against inaction: OSFI's E-21 compliance deadline, a cyber risk environment where legacy infrastructure creates measurable and worsening exposure, and an AI opportunity that is only accessible to institutions that have modernised their data architecture. The question for CTOs, COOs, and Heads of Digital Transformation is not whether to modernise — that decision has already been made by the regulatory environment. The question is how to execute with the right sequencing, the right integration strategy, and the right delivery partner.
Legacy application modernisation done correctly does not disrupt business operations. It creates the infrastructure that enables every subsequent competitive initiative — from AI-driven trading analytics to API-based fintech partnerships to real-time regulatory reporting. The banks that execute well in 2026 will not just meet their OSFI deadlines. They will build the technical foundation that compounds advantage across every product cycle that follows.
To commission a structured legacy modernisation assessment for your Canadian banking technology estate, engage VLink's delivery team today. Our banking modernisation specialists combine deep OSFI regulatory knowledge with proven execution methodology to deliver results without disrupting your operations.

Global Delivery Manager, VLink Inc.
Shivisha Patel serves as the Global Delivery Manager at VLink Inc., bringing a wealth of experience in program delivery and management, particularly in the insurance and banking sectors. She has a robust technical background with deep expertise in WebSphere MQ, WTX, IIB, middleware, and enterprise system integration.







 Shivisha Patel
Shivisha Patel