A breach is no longer just an IT event. It is a board-level, shareholder-level, regulator-level problem. Many banks are still running the wrong endpoint strategy for their risk profile. This guide helps you fix that.
Key numbers shaping this decision in 2026:
- 94% of CISOs say AI-driven defense is their top 2026 budget priority (Gartner, 2025)
- 2.4 million phishing emails targeted financial institutions in the first half of 2025 alone. 30% targeted the C-Suite (Darktrace, 2026)
- 80% of breaches involve stolen credentials. Identity integration in your EDR is not optional (CrowdStrike Global Threat Report, 2025)
- Mean Time to Recovery (MTTR) is now what regulators and boards ask about first — not just detection rates
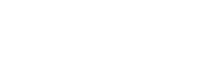
Why Endpoint Decisions Are Different in Financial Services
Generic EDR comparisons focus on detection scores and feature checklists. That is the wrong frame for a bank, credit union, or capital markets firm.
In financial services, endpoint security is infrastructure. It affects regulatory exams, audit outcomes, disclosure timelines, and customer trust.
Regulatory Pressure: FFIEC, GLBA, PCI DSS, NYDFS, and SEC
The FFIEC Cybersecurity Assessment Tool scores endpoint controls as part of your risk maturity. GLBA requires ongoing protection of personal financial data — including on endpoints. PCI DSS 4.0 demands continuous monitoring of card data environments.
NYDFS 23 NYCRR 500 requires detailed audit logs and reporting within 72 hours of a material event. The SEC's rules push public firms to disclose incidents within four business days.
Your EDR platform sits at the center of all of this. If it cannot produce clean logs, support forensics, and export compliance-ready reports — it adds risk, not reduces it.
The Cost of Downtime
For a retail bank, an encryption event during business hours costs around $150,000 per hour in lost operations.
For a capital markets firm, trading floor downtime can exceed $1 million per minute at peak.
For a credit union, ransomware on branch endpoints triggers regulator notification, reputational damage, and member loss — all at once.
The case for premium EDR is about recovery speed and regulatory defensibility — not features.
MTTR Matters More Than MTTD in 2026
Mean Time to Detect (MTTD) was the key metric five years ago. Today, regulators, boards, and cyber insurers ask about MTTR — Mean Time to Recovery.
The question has shifted from 'did you catch it?' to 'how fast did you get back to normal?'
Each of the three platforms addresses MTTR differently. Your selection should match your Recovery Time Objectives (RTOs) and reporting obligations.
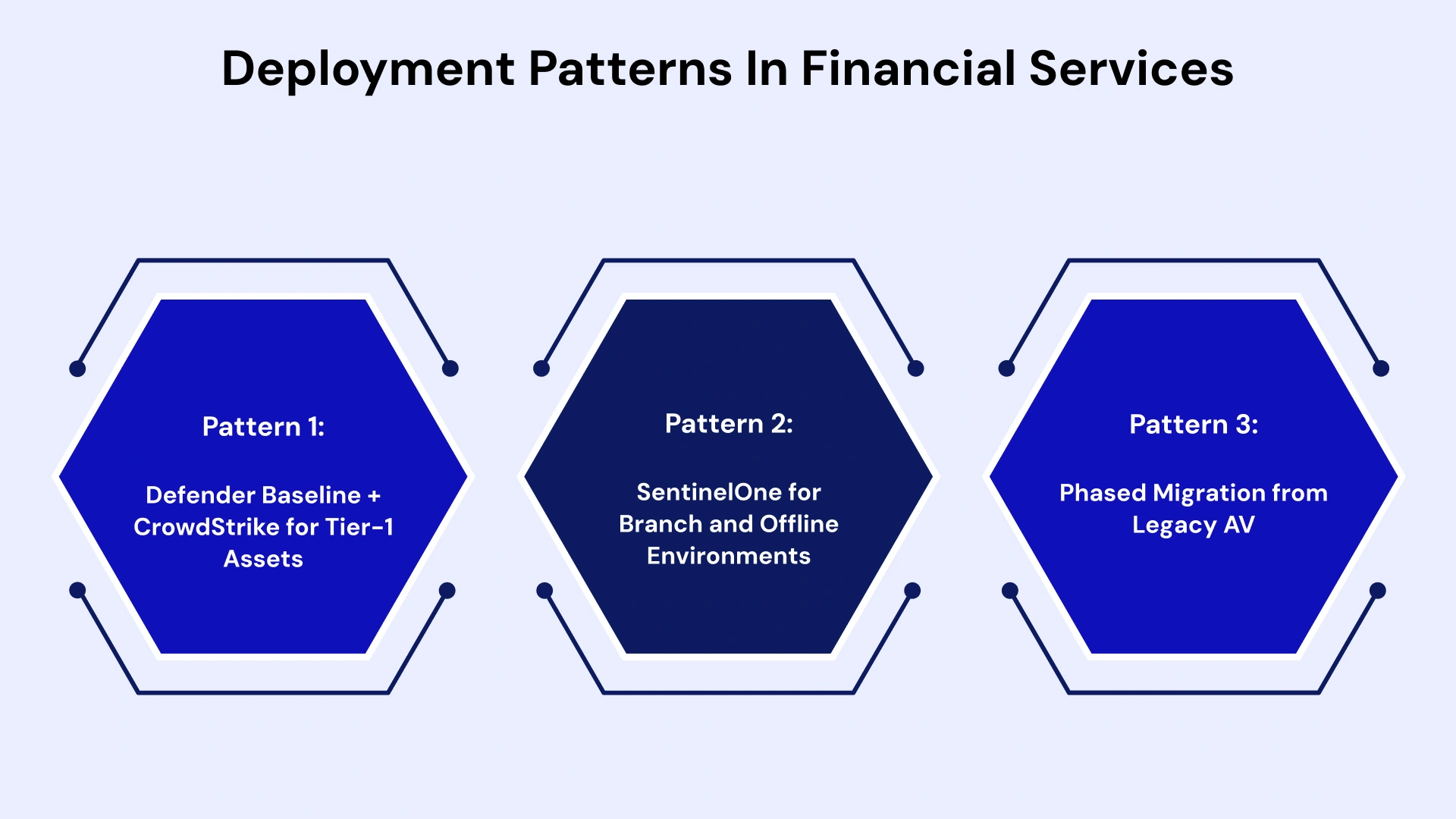
Quick Comparison: Defender vs CrowdStrike vs SentinelOne (Financial Services Lens)
Choosing between Microsoft Defender vs CrowdStrike vs SentinelOne usually depends on your current IT ecosystem and whether you prioritize automation, human-led investigation, or cost-efficiency.
| Criteria | Microsoft Defender | CrowdStrike Falcon | SentinelOne Singularity |
| Architecture | Cloud + OS-native (Windows-first) | Cloud-native, lightweight agent | On-device AI, works offline |
| Threat Intel Depth | Good — Microsoft global telemetry | Elite — Threat Graph, 300+ adversary profiles | Strong — AI-driven, growing library |
| Autonomous Rollback | Limited — manual steps required | Partial — Falcon Fusion automation | Native 1-Click Rollback — best in class |
| Compliance Reporting | Strong for Microsoft stack only | Excellent — full forensics and audit trail | Strong — Storyline gives full incident context |
| Data Residency | Azure US regions, configurable | Configurable — FedRAMP authorized | Configurable — US regions available |
| SOC Workload Impact | High without tuning | Moderate — high-fidelity alerts | Low — AI reduces alert volume by 60-70% |
| Pricing Posture | Included in M365 E5 — lowest entry cost | Premium — highest per-endpoint cost | Mid-tier — competitive for mid-market |
| Best FS Fit | Microsoft-heavy retail banks, insurers | Capital markets, wealth mgmt, Tier-1 banks | Credit unions, mid-market banks, lean SOCs |
Deep Dive: How Each Platform Fits Financial Services
Now, let’s explore each platform—Microsoft Defender vs CrowdStrike vs SentinelOne—in detail to understand their unique capabilities and cost structures.
CrowdStrike Falcon: Intelligence-Led Defense for High-Value Targets
CrowdStrike sets the benchmark for enterprise threat intelligence. Its Threat Graph processes over 2 trillion events per week. That gives it an adversary profile depth that Defender and SentinelOne cannot match.
In 2025, CrowdStrike hit 100% protection and detection scores in the MITRE ATT&CK Evaluations. That result matters when you are defending trading terminals or wealth management workstations.
Falcon goes beyond endpoint detection. Its Identity module watches Active Directory and Entra ID for credential abuse. This is critical. 80% of breaches start with stolen credentials.
OverWatch — CrowdStrike's managed threat hunting team — provides 24/7 proactive hunting. It is a real extension of your SOC. Institutions that cannot staff an in-house Tier 3 team find this valuable.
CrowdStrike earns premium consideration when:
- You are defending capital markets or wealth management workstations
- Your SOC has mature Tier 2-3 analysts who can act on Threat Graph data
- You face advanced persistent threats from nation-state actors
- You need the deepest forensic audit trail for regulatory defense
One area to evaluate carefully: CrowdStrike faced scrutiny after a 2024 sensor update caused widespread outages. The vendor has since restructured its update validation process. Review their current change control policies before deployment.
Pros: Known for having a very lightweight "single agent." It is widely considered the gold standard for threat hunting. Their Overwatch (managed hunting) service is highly regarded for catching "living off the land" attacks where hackers use legitimate tools.
Cons: It is often the most expensive option. The architecture is cloud-centric, meaning some advanced detection features are less effective if a device is completely offline.
Use Case: A Tier-1 bank with 50,000+ seats deployed CrowdStrike Falcon to unify identity and endpoint protection. A 2025 QR-code phishing campaign targeted their wealth management team. Falcon's identity correlation detected lateral movement before any financial data was touched.
SentinelOne Singularity: Autonomous Rollback for Lean SOC Teams
SentinelOne wins on efficiency. It's on-device AI works without a cloud connection. That matters for branch banking, ATM oversight, and disaster recovery scenarios where the network is down.
Its standout capability is native 1-Click Rollback. When ransomware hits, SentinelOne reverses the encryption using VSS-based snapshots. No cloud connection needed. No human required. No waiting for an analyst to respond.
No other platform in this comparison does this at the same level of automation.
Storyline technology correlates all telemetry into one incident view. Instead of triaging 500 individual alerts, your team sees one clear story. Forrester highlighted this in its Q1 2025 Wave as a key driver of alert fatigue reduction.
SentinelOne earns serious consideration when:
- Your SOC team is lean — 3 to 10 analysts
- You have remote or offline branch endpoints
- You want to reduce MSSP dependency or SOC headcount
- You are moving from legacy AV without building a full threat hunting practice
Pros: Its "Storyline" technology automatically connects the dots of an attack, making it easy for a junior analyst to see exactly what happened. The Rollback feature is a lifesaver—if ransomware encrypts files, S1 can often revert the changes to a healthy state automatically.
Cons: Because it is so automated, some "power users" find it less flexible for custom scripting compared to CrowdStrike. It operates at the kernel level, which can occasionally lead to resource spikes if not tuned.
Use Case: A North American credit union deployed SentinelOne across 47 branches. A zero-day exploit hit one branch endpoint during off-hours. The agent rolled back the encryption before the on-call analyst received the alert. Recovery time: under 4 minutes. No data was lost. No regulator notification was triggered.
Microsoft Defender for Endpoint: Ecosystem Leverage and TCO Optimization
Microsoft Defender is no longer a placeholder. For organizations deep in the Microsoft 365 and Azure stack, Defender XDR is a capable platform. Its inclusion in E5 licensing makes the cost case easy to present.
Defender's real strengths: native integration with Microsoft Sentinel, Entra ID, Purview, and the Microsoft Security Graph. This creates a unified data layer that no standalone EDR can replicate inside the Microsoft ecosystem. Attack Surface Reduction (ASR) rules and Intune integration give security teams strong control without extra agents.
Despite being bundled with Microsoft 365 E5, Microsoft Defender isn't truly "free." Over three years, its total cost of ownership (TCO) often exceeds premium alternatives like CrowdStrike due to high operational overhead. Hidden expenses—including specialist salaries, labor-intensive manual tuning, and complex SIEM integration—combined with slower response times, frequently make this "included" tool the more expensive long-term investment.
But Defender has real gaps in financial services:
- Non-Windows coverage — Linux and macOS — produces telemetry gaps vs CrowdStrike and SentinelOne
- Licensing complexity — the full Defender XDR stack needs E5 or add-ons that can match the cost of premium EDR when fully scoped
- Heavy tuning required — out-of-the-box Defender generates high false-positive rates in complex environments
- No native autonomous rollback — ransomware recovery is more manual and takes longer
The honest assessment: Defender alone may work for a Microsoft-heavy retail bank with low regulatory complexity and a skilled internal team. It is rarely enough as the sole control for capital markets, wealth management, or any institution under active NYDFS examination.
Regulatory and Audit Readiness Comparison
This section covers the critical details most EDR comparisons overlook—the exact factors your GRC team, external auditors, and regulators prioritize when evaluating Microsoft Defender vs CrowdStrike vs SentinelOne.
Mapping to FFIEC, GLBA, PCI DSS, and NYDFS Controls
| Regulatory Requirement | Microsoft Defender | CrowdStrike | SentinelOne |
| FFIEC CAT — Endpoint Monitoring | Meets baseline with tuning | Exceeds baseline | Exceeds baseline |
| GLBA — Personal Data Protection | Adequate for M365 environments | Strong cross-platform | Strong cross-platform |
| PCI DSS 4.0 — Continuous Monitoring | Needs Microsoft Sentinel add-on | Native and real-time | Native and real-time |
| NYDFS — 72-Hour Incident Reporting | Manual log export required | Automated reporting ready | Automated via Storyline |
| SEC — Material Incident Disclosure | Sentinel integration needed | Falcon Forensics ready | Storyline audit trail included |
| SOX — Audit Trail Integrity | Adequate with full E5 stack | Excellent — tamper-evident logs | Excellent — immutable log chain |
Log Retention, Forensics, and Chain-of-Custody
CrowdStrike retains up to 90 days of raw telemetry with tamper-evident logs. This is key for post-incident forensics during regulatory exams.
SentinelOne's Storyline gives a complete, immutable chain of events — from the initial vector to lateral movement to encryption or data loss. Regulators and incident responders get a clear picture fast.
Microsoft Defender can match this with Microsoft Sentinel, but it requires deliberate architecture and extra cost.
Data Residency and Cross-Border Telemetry
All three platforms offer US-based data residency. CrowdStrike holds FedRAMP authorization. This matters for institutions with government relationships or those preparing for federal oversight.
SentinelOne and Microsoft both support GDPR-compliant handling for firms with international operations. Any institution under NYDFS should confirm telemetry routing agreements with their vendor in writing — and document this for exam readiness.
SOC Integration and Operational Impact
The effectiveness of these platforms in a financial SOC (Security Operations Center) isn't just about catching threats—it’s about how they integrate into your workflow to meet the strict 24-hour reporting windows required by regulations.
Integration with Sentinel, Splunk, and QRadar
All three platforms connect to major SIEM and SOAR stacks — but the depth differs.
- Microsoft Defender integrates natively with Microsoft Sentinel. It is plug-and-play for M365 SOCs. Splunk and QRadar connections exist but are less seamless.
- CrowdStrike provides pre-built connectors for Splunk, QRadar, Sentinel, and most major SOAR platforms. Falcon Fusion adds internal SOAR capabilities and reduces dependency on external tools.
- SentinelOne connects via its Singularity Marketplace with 300+ third-party integrations. Its SIEM connectors are well-documented and work well in financial SOC environments.
Alert Volume, False Positives, and Analyst Fatigue
This is where the platforms diverge the most in practice.
- Out-of-the-box, Microsoft Defender produces high false-positive volume in complex environments. It needs dedicated tuning time.
- CrowdStrike's alerts are high-fidelity but fewer. Acting on them well requires Tier 2 or Tier 3 analyst skills.
- SentinelOne's Storyline correlation cuts raw alert volume by 60 to 70%. For lean teams, this is a game-changer.
Note:- Charlotte AI (CrowdStrike) and Purple AI (SentinelOne) both allow analysts to query telemetry using plain language. Both vendors report reductions of up to 40 analyst hours per week per platform (2025, vendor-reported data).
Using EDR Signals for Fraud and Insider Threat Teams
Your EDR data has value beyond the security operations center.
Unusual after-hours access to sensitive endpoints, odd file access patterns, and credential misuse alerts can feed financial crime and HR investigation workflows. CrowdStrike's Falcon Insight and SentinelOne's Ranger network visibility both provide the depth needed for cross-functional use cases.
Cost, TCO, and Risk-Adjusted ROI for a 10,000-Endpoint Bank
For a Tier 2 bank with 10,000 endpoints, the financial decision isn't just about the "price per seat"—it’s about tool consolidation versus specialized resilience. In 2026, Gartner estimates that firms prioritizing platform consolidation can reduce security incidents by 50%, a key driver for Risk-Adjusted ROI.
License Cost vs Operational Cost
The license cost is the least important number in your decision. The full picture looks like this:
| Cost Factor | Microsoft Defender (E5) | CrowdStrike Falcon | SentinelOne Singularity |
| License (per endpoint/year, est.) | ~$12–18 (blended E5 cost) | ~$65–85 (Falcon Elite) | ~$45–60 (Singularity Complete) |
| Setup and Tuning Hours (Year 1) | High — 200 to 400 hrs | Moderate — 80 to 160 hrs | Low — 40 to 80 hrs |
| Ongoing SOC Hours (Monthly) | High — needs senior FTEs | Moderate — OverWatch reduces the need | Low — AI handles Tier 1 and 2 triage |
| Incident Response Integration | Needs Sentinel and manual steps | Native with Falcon IR modules | Native with Storyline and rollback |
| 3-Year TCO (10K endpoints, est.) | $3.2M to $4.8M (full stack) | $4.5M to $6.5M (all-in) | $3.0M to $4.2M (all-in) |
Note: These are directional estimates based on industry benchmarks and public pricing data. Actual costs depend on your licensing agreements, SOC staffing model, and existing infrastructure.
Ransomware Scenario Modeling
Use this formula to model the total cost of ownership for your environment:
TCO = (License x Endpoints) + (SOC Hours x Hourly Rate) + (Breach Probability x Breach Cost)
Here is what the numbers look like for a 10,000-endpoint regional bank:
- Estimated breach cost for a regional bank: $4.7M (IBM Cost of Data Breach Report, 2025 — ibm.com/reports/data-breach)
- Annual breach probability with legacy AV: ~12%. With modern EDR: 3 to 5%
- At 4% breach probability and $4.7M breach cost, expected annual loss exposure = $188,000
- Premium EDR cuts that probability to ~2%, saving $94,000 per year in expected breach cost — before fines, remediation, or reputational damage
- The risk-adjusted ROI of premium EDR is positive for almost any institution processing more than $500M in annual transactions.
When Does Defender Alone Make Sense?
Defender-only works if: your environment is 95%+ Windows and M365, your team has dedicated Defender expertise, your regulatory exposure is low, and your board and insurers accept the risk posture.
For most institutions above $1B in assets, Defender alone is a gap that regulators and cyber insurers are no longer willing to accept.
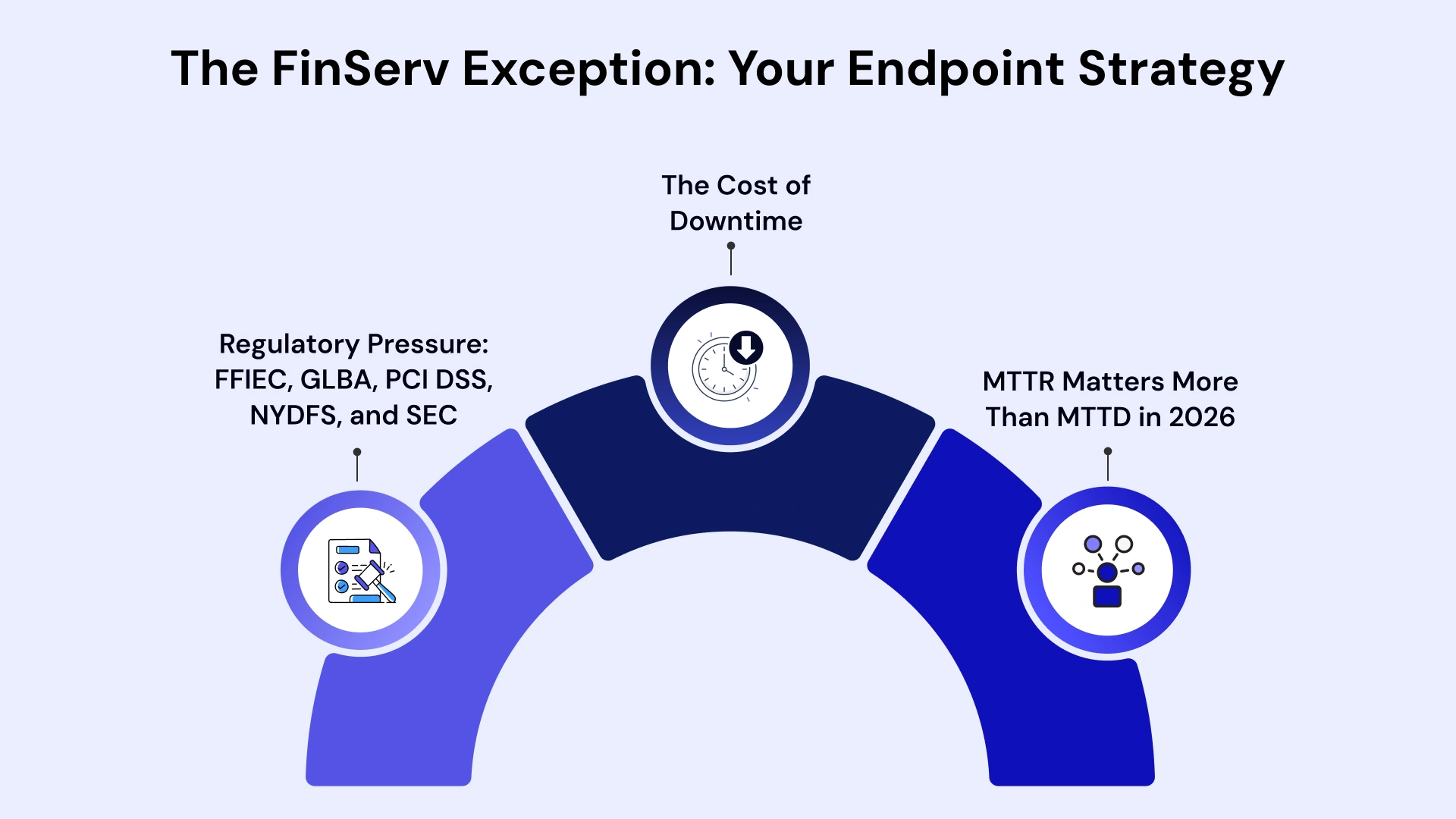
Common Deployment Patterns in Financial Services
In 2026, we see three dominant architectural patterns tailored to specific banking needs.
Pattern 1: Defender Baseline + CrowdStrike for Tier-1 Assets
Many larger institutions run Defender across standard workstations. They use CrowdStrike on high-risk endpoints — trading terminals, privileged admin workstations, SWIFT infrastructure, and executive devices.
This hybrid approach controls cost while directing premium telemetry where risk is highest. Coexistence of Defender and CrowdStrike is supported and well-documented by both vendors.
Pattern 2: SentinelOne for Branch and Offline Environments
SentinelOne's offline autonomous capability makes it the default for branch networks with spotty connectivity, ATM support infrastructure, and remote endpoints.
Many institutions deploy SentinelOne at the branch level and CrowdStrike or Defender in centralized data center environments.
Pattern 3: Phased Migration from Legacy AV
No institution moves from legacy AV to premium EDR overnight.
A practical approach: deploy EDR in passive monitoring mode for 30 to 45 days to baseline normal behavior. Tune exclusions and policies. Activate prevention in test groups. Roll out organization-wide over 90 days.
Both CrowdStrike and SentinelOne publish migration playbooks. Change control and performance validation are critical in core banking and payment processing environments.
CISO Decision Framework: The Resilience-First Model
Use this four-step process before presenting your EDR recommendation to the board or preparing for your next regulatory exam.
Step 1: Environment and OS Mix Assessment
Calculate the percentage of non-Windows endpoints in your environment. If it exceeds 30% — Linux servers, macOS executive devices, legacy systems — Defender will produce material telemetry gaps.
CrowdStrike and SentinelOne both provide stronger cross-platform coverage.
Step 2: SOC Maturity Audit
Does your SOC have 24/7 Tier 3 threat hunting capability?
If yes — CrowdStrike's telemetry depth is an accelerant. If no — and most mid-market institutions do not — SentinelOne's automation replaces significant manual effort. CrowdStrike's OverWatch fills the hunting gap at an added cost.
Step 3: Ransomware Rollback Simulation
Run a simulated ransomware exercise. Time your team's recovery from detection to full remediation.
If the answer exceeds four hours, you have a regulatory and operational risk gap. Neither Defender alone nor a manual playbook can reliably close it. SentinelOne's autonomous rollback consistently achieves sub-five-minute recovery in controlled environments.
Step 4: Regulatory and Board Alignment Score
Before selecting a platform, score each vendor against your specific obligations. Use NYDFS, FFIEC, PCI DSS, and SEC disclosure timelines as your criteria.
Document your scoring. It becomes your regulatory defense artifact if your selection is challenged during an exam.
Final Verdict: Platform Selection by Financial Sub-Vertical
Now, let’s explore tailored platform recommendations that align specifically with the unique compliance mandates and operational scale of each financial sub-vertical, from community credit unions to global investment firms.
| Sub-Vertical | Recommended Approach | Primary Rationale |
| Retail Bank ($1B–$10B assets) | Defender baseline + SentinelOne on critical assets | Cost balance, lean SOC efficiency, offline branch coverage |
| Capital Markets / Trading | CrowdStrike Falcon — complete stack | Threat intelligence depth, identity integration, OverWatch hunting |
| Wealth Management | CrowdStrike or SentinelOne + Defender baseline | High-value client data, sophisticated threats, regulatory scrutiny |
| Credit Union | SentinelOne Singularity | Lean SOC automation, branch offline support, competitive pricing |
| Tier-1 Bank (50K+ endpoints) | CrowdStrike + Defender coexistence | Best-in-class hunting on priority assets, Defender scale for standard endpoints |
| Digital-First Fintech | SentinelOne or CrowdStrike (cloud-native stack) | Cloud-native alignment, API-first integration, rapid deployment |
| Insurance Provider (M365 heavy) | Microsoft Defender XDR — full stack | E5 leverage, Purview integration, homogeneous Windows environment |
The right answer is not a vendor. It is a strategy.
The most resilient financial institutions in 2026 run layered endpoint architectures. They use each platform where it delivers the most value. They maintain regulatory defensibility at every layer. And they build recovery speed into their security design from day one.
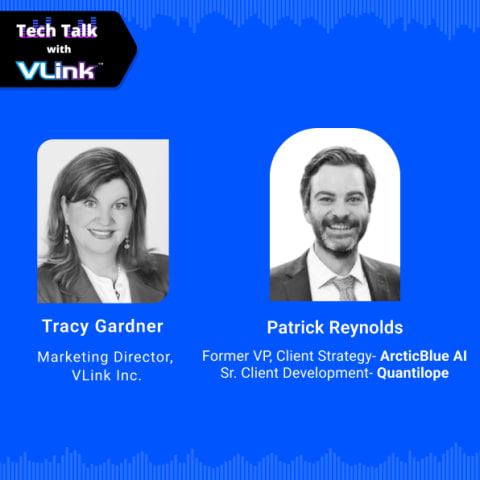
Future-Proof Your Business with VLink's Microsoft Solutions
Selecting the right EDR platform is a strategic decision. Deploying it correctly in a regulated financial environment takes a different kind of expertise.
VLink's Microsoft business solutions have supported financial institutions across retail banking, capital markets, insurance, and fintech. We help CISOs evaluate, implement, and manage endpoint security programs that hold up under regulatory scrutiny.
Our dedicated team brings direct experience with:
- EDR platform assessments and vendor-neutral competitive evaluations for CISOs
- Microsoft Defender, CrowdStrike, and SentinelOne implementation and migration
- Managed SOC integration with Microsoft Sentinel, Splunk, and QRadar
- Regulatory readiness support for NYDFS, FFIEC, PCI DSS, and SEC compliance
- Board-ready risk modeling and security investment justification frameworks
We do not have a preferred vendor. We match your environment, your regulatory profile, and your SOC maturity to the platform that delivers the best risk-adjusted outcome. Our Managed SOC services provide ongoing monitoring and threat response for institutions that want expert coverage without building it from scratch.
Ready to align your security strategy? Contact our team to schedule a technical discovery session and determine the best fit for your institutional needs.
Conclusion
Microsoft Defender, CrowdStrike, and SentinelOne are not the same tool. Each reflects a different security philosophy: ecosystem integration, intelligence-led offense, and autonomous resilience.
For financial services CISOs, the decision is not which vendor is best in the abstract. It is the combination of capabilities that fits your regulatory obligations, your SOC maturity, your environment, and your recovery time requirements.
Start with your MTTR target. Work backward to the platform architecture that achieves it. Document your rationale in a form that a regulator, a board member, and a cyber insurer can all follow.
That is what a resilience-first endpoint strategy looks like in 2026.

Vice President, Strategy – VLink Inc.
Sambhavi Gopalakrishnan is the Vice President of Strategy at VLink Inc., bringing over a decade of experience in IT leadership, project implementation, and strategic growth. She possesses a strong foundation in technical project management and pre-sales, driving innovation and business transformation at VLink.









 Shivisha Patel
Shivisha Patel