Picking the wrong software vendor is expensive. For a bank, it can also be dangerous. A bad vendor choice can trigger compliance gaps, failed audits, and years of costly rework. The stakes are high at every level of the organization.
Here are three numbers that show the scale of the problem:
This guide fixes that. It gives you a clear, banking-specific framework for custom software development vendor. You will get an RFP structure, a weighted scoring model, a due diligence checklist, and a list of red flags to eliminate vendors early.
This is built for CTOs and VPs of Digital Banking who need to get this right — the first time. Let’s start!
Why Custom Software Development Vendor Selection Is Harder for NA Banks in 2026
In 2026, the landscape for North American (NA) banks selecting custom software development vendors has shifted from a race for innovation to a complex game of high-stakes "adaptation." While the technology is more powerful than ever, the hurdles to actually deploying it have multiplied.
Here is why custom software development vendor selection is significantly harder for NA banks this year:

The 60/40 IT Budget Trap
Most banks are stuck in the same pattern. The majority of IT spend goes to keeping old systems running — patches, upgrades, compliance fixes.
That leaves very little budget for real transformation. When you finally get approval for a new project, you cannot afford to waste it on the wrong vendor.
Top-performing banks are now targeting a shift: bring maintenance spending below 45% by using AI-driven refactoring and custom automation tools. Vendors who cannot support that goal are not partners. They are obstacles.
Regulatory Pressure and Third-Party Risk Scrutiny
Regulators are moving fast. The OCC, FDIC, Federal Reserve, and OSFI have all sharpened their third-party risk management (TPRM) rules in the last 18 months.
If a vendor fails a compliance audit, your bank shares that risk.
New Nacha fraud monitoring rules take effect in March and June 2026. They require built-in velocity checks and anomaly detection in any payment-related software. On top of that, NIST is finalizing post-quantum encryption standards — and vendors need a roadmap for that too.
Vendors who treat compliance as a checkbox will not survive your risk committee's review. You need partners who treat regulatory depth as a strength.
The Hidden Cost of Getting Vendor Selection Wrong
The visible cost of a bad vendor is the contract value. The hidden cost is what comes after.
Think about delayed timelines, failed integrations, compliance gaps, and re-platforming fees. One mid-size US regional bank spent 18 months and over $5 million unwinding vendor lock-in from a core-adjacent SaaS deal. The vendor promised speed. They delivered technical debt.
A strong vendor selection process stops this before it starts.
Custom Software Development Vendor vs. Generic Banking Platform: Which Is Right for Your Bank?
Choosing between a custom software development vendor and a generic banking platform (SaaS) is essentially a choice between buying a tailored suit or buying off-the-rack. One fits your specific curves perfectly, while the other is ready to wear today at a lower entry price.
When Off-the-Shelf Makes Sense
Generic banking platforms work well for standard, non-differentiating functions. Basic account management, standard payment rails, and vanilla reporting can fit a pre-built product. The risk is low when the function is easy to swap out if the vendor relationship breaks down.
When Custom-Only Is the Right Call
Custom software wins when the function gives you a competitive edge. It also wins when regulatory requirements are complex, when your existing stack has unique integration needs, or when you need full IP ownership to stay agile.
If a third-party roadmap controls how fast you can move, that is a strategic problem. It just looks like a procurement decision.
Decision Matrix: Core vs. Edge vs. Differentiation Systems
| System Type | Buy SaaS | Customize Platform | Custom Build |
| Core System Replacement | High Risk | Medium Risk | Recommended |
| Digital Channel (Mobile/Web) | Limited Fit | Good Fit | Best Fit |
| Compliance / Regtech Tools | Medium Risk | Medium Risk | Recommended |
| AML / Fraud Detection | Limited Fit | Medium Fit | Best Fit |
| Customer Onboarding Flows | Good Fit | Good Fit | Best Fit |
Real example: A Tier-2 regional bank rejected a generic loan SaaS. Instead, they chose a custom composable architecture. The vendor built a modular loan engine, connected it to their FIS core via a custom API layer, and transferred 100% of the IP to the bank.
Loan approval time dropped from 12 days to 48 hours. The bank now calls it their "Speed-Lend" engine — and markets it as a competitive advantage.
Step-by-Step Framework: How to Select a Custom Software Development Vendor for Banking
Use these seven steps in order. Skipping any one of them is where most banks go wrong.

1. Define regulatory and architectural constraints first. Map your TPRM requirements, data residency rules, and core integration targets before you write a single RFP question.
2. Pre-qualify vendors on operational resilience. Ask for deployment frequency, change failure rate, and mean time to recovery (MTTR). If a vendor cannot give you hard numbers, they are not ready for a regulated environment.
3. Align internal stakeholders before the RFP goes out. Risk, InfoSec, procurement, and business lines must agree on priorities upfront. Misalignment here becomes a contract dispute 18 months later.
4. Issue a banking-specific RFP. Not a generic IT template with banking words added. The document should test whether vendors truly understand your operating environment.
5. Use a weighted scoring matrix. Remove gut-feel from the evaluation. Score vendors against pre-agreed criteria before any group discussion happens.
6. Run a sandbox PoC or architecture workshop. Ask finalists to solve a real integration challenge against your actual stack. Presentations show what vendors want you to see. Workshops show what they can actually do.
7. Negotiate IP ownership, SLAs, and exit terms before signing. Make sure you own the code, can access source files on demand, and have a clear exit path if the relationship ends.
Vendor Risk, Compliance & Regulatory Expectations in Banking IT Projects
Below is a breakdown of current regulatory expectations and the framework for managing project risk.
Third-Party Risk Management (TPRM) Requirements
TPRM is no longer just a compliance box. It is a board-level concern.
The OCC's third-party risk guidance (OCC 2023-17) and OSFI's B-10 guidelines require banks to assess, monitor, and document vendor relationships at every stage. Your vendor selection process must produce audit-ready records from day one — not after a regulator asks for them.
Security & Compliance: SOC 2, PCI DSS, GLBA, and Data Residency
Every shortlisted vendor must provide evidence of SOC 2 Type II certification. PCI DSS compliance is required where applicable. GLBA-aligned data handling is non-negotiable.
For Canadian institutions, data residency within Canada is increasingly required for any customer-facing system. Do not accept verbal commitments. Require current audit reports with valid dates.
The DORA Gateway Concept
Think of this as a resilience screening step you run before you evaluate features.
Borrowed from the EU's Digital Operational Resilience Act, a DORA-style screen tests vendors on three key metrics: deployment frequency (how often they ship to production), change failure rate (what percentage of deployments need hotfixes), and incident response time.
A vendor who cannot answer these with real data is not production-ready for a regulated bank.
Cloud & Offshore Delivery Risk
Offshore delivery can be cost-effective. But for North American banks, it also introduces data residency risk, cross-border data transfer obligations, and conflicts with state-level privacy laws.
Require vendors to document exactly where data is processed, stored, and backed up. Make sure subcontractor relationships are disclosed and held to the same security standards as the primary contract.
Minimum compliance checklist — require verifiable evidence for each item:
- Audited SDLC with documented change management process
- Deployment frequency metrics for the past 12 months
- Change failure rate and MTTR from production incidents
- SOC 2 Type II certification (current, not expired)
- Data localization compliance documentation
- Business continuity and disaster recovery certifications
- Subcontractor disclosure and security governance map
Banking IT Vendor Due Diligence Checklist (CTO Edition)
Use this checklist during shortlisting. Every item needs a documented, verifiable answer before a vendor moves to the RFP stage.
Domain Expertise
- At least two North American bank references at a comparable asset size
- Proven integration experience with FIS, Fiserv, Jack Henry, or Temenos
- Named team members with real banking domain experience — not just general fintech background
Architecture
- Microservices or composable architecture capability
- API-first design with documented standards
- AI and automation readiness — can their stack support agentic workflows?
- A roadmap or current approach to quantum-safe encryption
Delivery & Governance
- Dedicated team retention rate above 85% — anything lower is a project risk
- Managed outcome delivery — can they commit to business KPIs, not just milestones?
- Documented standards for code review, test coverage, and technical documentation
Financial & Operational Stability
- No single client should represent more than 30% of vendor revenue
- Adequate professional liability and cyber insurance in place
- Clear ownership structure with no undisclosed acquisition or restructuring activity
RFP Template for Banking Software Development
Choosing the right workflow engine requires an Appian vs Pega vs IBM BPM comparison based on bank size, use cases, and IT maturity.
Businesses evaluating RFP Template for Banking Software Development should also consider banking workflow platform comparison to improve execution quality, scalability, and long-term operational resilience.
A banking software RFP is a formal document. It asks qualified vendors to describe how they would solve your specific problem.
Unlike a generic IT RFP, a banking version must encode regulatory context, integration complexity, and compliance obligations into the questions themselves. The goal is not just to gather proposals for banking software development services. The goal is to test whether a vendor actually understands your world.

Nine sections every banking software RFP must include:
1. Executive Summary — describe the strategic objective and the problem being solved through ideal financial software development services
2. Business Objectives — define measurable outcomes, not feature lists
3. Regulatory Context — name the applicable regulations, oversight bodies, and compliance requirements the vendor must address in their response
4. Technical Architecture Requirements — API standards, integration targets, data models, and scalability expectations
5. Security & Compliance — SOC 2, PCI DSS, GLBA, data residency, and penetration testing requirements
6. Delivery Governance — methodology expectations, sprint cadence, escalation paths, and change management process
7. SLA & Support — uptime targets, incident response tiers, and escalation timelines
8. Pricing Model — time-and-material vs. fixed-price vs. managed outcome; IP ownership terms must be explicit
9. Evaluation Criteria & Weights — show vendors how they will be scored; transparency removes ambiguity and gets better responses
Evaluation Criteria & Weighted Scoring Model for Banking Vendors
Below is a standardized framework for building an objective, audit-ready scoring model.
Sample Weight Distribution (2026 Model)
| Evaluation Criteria | Weight | What to Look For |
| Domain Expertise | 20% | North American bank references, core integration history, regulatory depth |
| Architecture & Scalability | 20% | Microservices readiness, API-first design, AI workflow support |
| Security & Compliance | 20% | SOC 2 Type II, PCI DSS, GLBA, incident response capability |
| Delivery Track Record | 15% | On-time delivery history, defect rates, reference call results |
| Commercial Model & IP Terms | 15% | IP ownership clarity, pricing transparency, exit clause terms |
| Cultural Fit & Governance | 10% | Communication quality, risk escalation culture, stakeholder alignment |
Why Weighted Scoring Reduces Risk
Weighted scoring removes bias. It forces your team to agree on criteria before seeing any proposals. This reduces the influence of strong presenters who have weak delivery records.
It also creates an audit trail. Your risk committee and procurement team will ask how you made the decision. A documented scoring model gives you a clear answer.
One North American bank skipped this step. They approved a vendor based on a strong demo. The team missed a critical AML workflow gap — caught only in UAT. The fix cost $380,000 and pushed the launch back six months.
A pre-agreed scoring model prevents exactly this.
Modern Banking Selection Scenarios (Use-Case Based)
To illustrate how the scoring model and regulatory framework apply in the real world, here area few high-stakes "2026 scenarios" that banks are currently navigating.
Digital Banking Modernization
For digital channel work — mobile apps, web banking, open banking APIs — look for vendors with strong UX research skills and API gateway experience.
They must be able to separate the presentation layer from the legacy backend. This lets you update the customer experience without touching core systems. Ask for examples of composable architecture they have shipped in production.
Core System Refactoring — Hollowing Out the Core
This is the most complex engagement a bank can run. The vendor must prove they can work inside a live production environment.
They need to build abstraction layers that intercept core functions one step at a time. They must transfer IP cleanly at each phase. Demand a phased delivery roadmap with clear go/no-go gates. Never accept a multi-year, big-bang project plan.
Cloud Migration & Data Fabric Initiatives
Cloud migration in banking is a regulatory challenge as much as a technical one.
Vendors must show experience with hybrid cloud architectures, data lineage tools, and integration with existing data warehouses. Ask directly how they handle personally identifiable information (PII) in transit and at rest across cloud zones.
Tokenization & AI-Driven Automation Readiness
Tokenized assets in banking hit $25 billion in 2025 — a 245x increase since 2020. This is not a future trend. It is a current operating reality.
Vendors pitching AI-powered automation or tokenization readiness must be specific. Ask for production examples, not roadmap slides. For tokenization, require demonstrated experience with real settlement and legal frameworks — not just blockchain technology knowledge.
Red Flags When Evaluating Banking Software Vendors
Each item below is a warning sign. One confirmed red flag warrants a deeper look. Two or more should end the conversation.
- Vague or deflected answers about compliance certifications or audit results
- No verifiable references from North American banks at a comparable size
- No IP transfer clause in their standard contract — ownership stays with the vendor by default
- Heavy reliance on unnamed subcontractors with no visibility into their qualifications or security posture
- Refusal to commit to business outcome KPIs — only willing to commit to deliverable milestones
- Change failure rate above 15%, or inability to provide this metric at all
- Team retention below 80% — high turnover destroys institutional knowledge mid-project
- No documented process for knowledge transfer, handover documentation, or exit planning
What North American Banks Look for When Switching IT Vendors
The top reasons North American banks replaced their technology vendors in 2025 and 2026 are clear:
- Slow and unpredictable delivery cycles
- Cost overruns on fixed-price contracts
- Integration failures with core systems
- Weak understanding of regulatory requirements
- IP ownership disputes and exit blockers
What CTOs Prioritize in a Replacement Vendor
When CTOs describe what they need from a new vendor, three themes come up every time.
- First: predictable delivery. They want outcome-based commitments, not milestone reports.
- Second: code ownership. They want clean documentation and handover standards built into the contract.
- Third: modern architecture. They refuse to trade one generation of technical debt for another.
The shift from SaaS licensing to custom build-and-own is accelerating. Banks want their software to be a balance-sheet asset—not a recurring subscription.
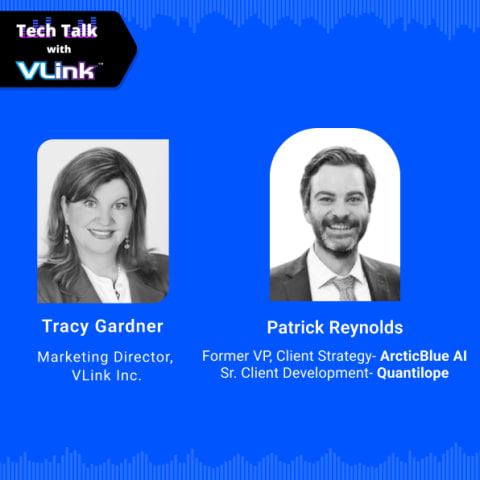
Scale Faster with VLink: Ideal Services for Banks
VLink is a custom software development services partner built for North American banks and financial institutions.
We do not sell platforms. We do not push pre-built modules. Every solution we build is designed around your stack, your regulatory obligations, and your strategic goals. You own the IP. Always.
Our banking technology practice covers core system refactoring, digital channel modernization, AI and automation integration, cloud migration, and compliance engineering. Our engineers have direct integration experience with FIS, Fiserv, Jack Henry, Temenos, Fedwire, ACH, and major card processors.
What sets VLink apart:
- Banking-specific domain depth — not generic fintech experience
- Managed outcomes delivery model with KPI accountability
- Build-to-Own approach — your software becomes a proprietary asset
- Free RFP review and vendor shortlisting support for active evaluations
- Verified North American banking references available under NDA
Ready to Simplify Your Vendor Selection Process?
Choosing the right partner is the most critical step in your digital transformation journey. If you’re currently drafting an RFP or evaluating potential vendors, don't navigate the complexities alone. Connect with a VLink Expert to turn your checklist into a reality.
Conclusion
Selecting a custom software development vendor for your bank is not a procurement task. It is a risk management decision.
The vendor you choose will touch your core systems, your customer data, and your regulatory obligations. Getting it wrong is expensive. Getting it right requires a structured process — not intuition.
Use the steps in this guide. Issue a banking-specific RFP. Score vendors using a weighted matrix. Run a sandbox PoC before you commit. Negotiate for IP ownership and clean exit terms. Remove any vendor who cannot back up their claims with real data.
The banks that win the next decade will not just move fast. They will build on the right foundation — with the right partners — and own what they build.

Global Delivery Manager, VLink Inc.
Shivisha Patel serves as the Global Delivery Manager at VLink Inc., bringing a wealth of experience in program delivery and management, particularly in the insurance and banking sectors. She has a robust technical background with deep expertise in WebSphere MQ, WTX, IIB, middleware, and enterprise system integration.










 Shivisha Patel
Shivisha Patel